Knox Security
With Knox enabled, Knox now handles authentication when accessing the UIs and REST together. Basic authentication is still an option for making requests directly to the REST application. Any request to the UIs must go through Knox first and contain the proper security token.
If a valid token is not found, Knox will redirect to the Knox SSO login form. Once a valid token is found, Knox will then redirect to the original url and the request will be forwarded on. Accessing the REST application through Knox also follows this pattern. The UIs make REST requests this way with Knox enabled since they no longer depend on Express to proxy requests. The context path now determines which type of request it is rather than the host and port.
REST still requires authentication so a filter is provided that can validate a Knox token using token properties and a Knox public key. The REST application also supports Basic authentication. Since both Knox and the REST application should use the same authentication mechanism, LDAP authentication is required for the REST application.
Roles are mapped directly to LDAP groups when Knox is enabled for REST. LDAP group names
are converted to upper case and prepended with ROLE_. For example, if a
user's groups in LDAP were user and admin, the
corresponding roles in REST with Knox enabled would be ROLE_USER and
ROLE_ADMIN.
The following diagram illustrates the flow of data for the various types of requests when Knox is enabled:
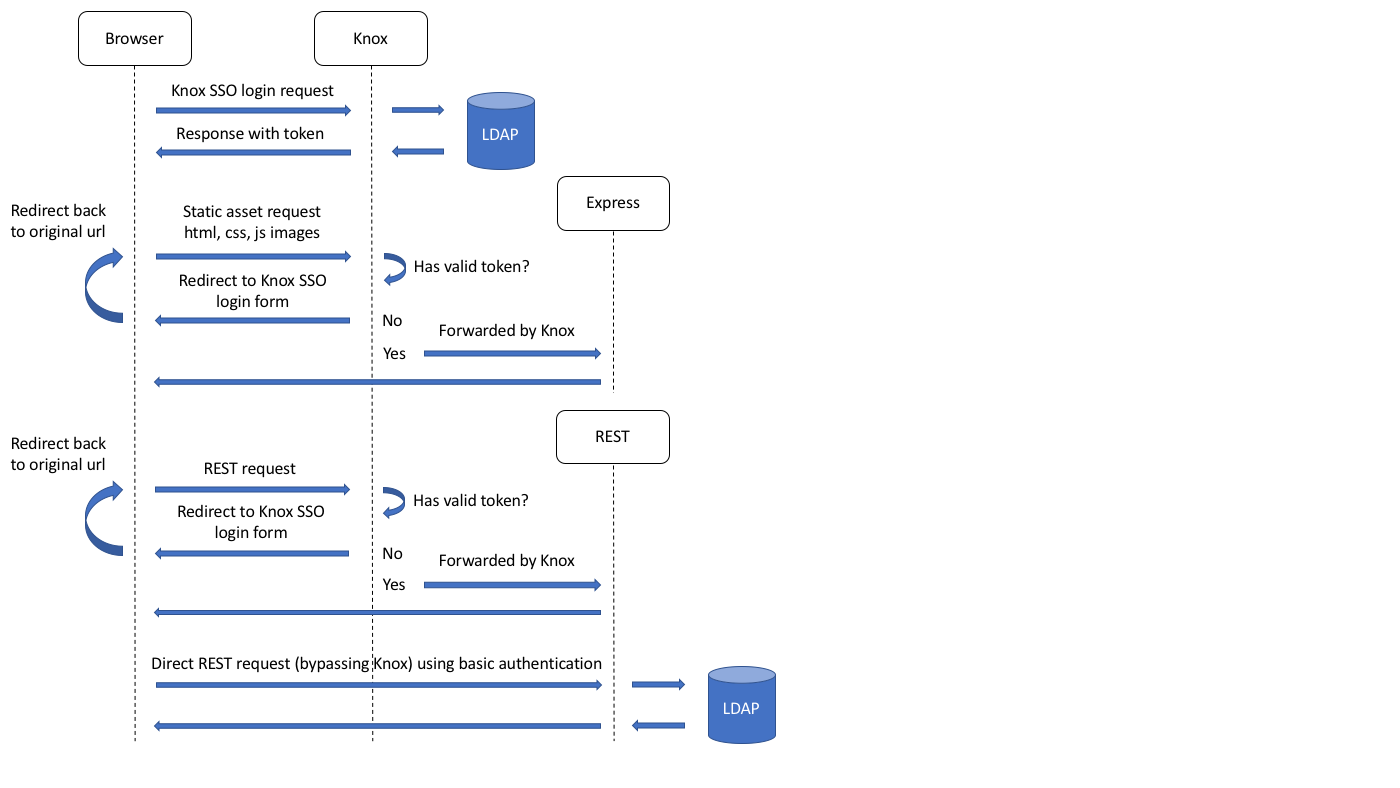
Note how the flow diagrams for Static asset requests and Rest requests (through Knox) are identical.
