Restricted Controller Service Created in Root Process Group
In this first example, sys_admin creates a KeytabCredentialsService controller service at the root process group level.
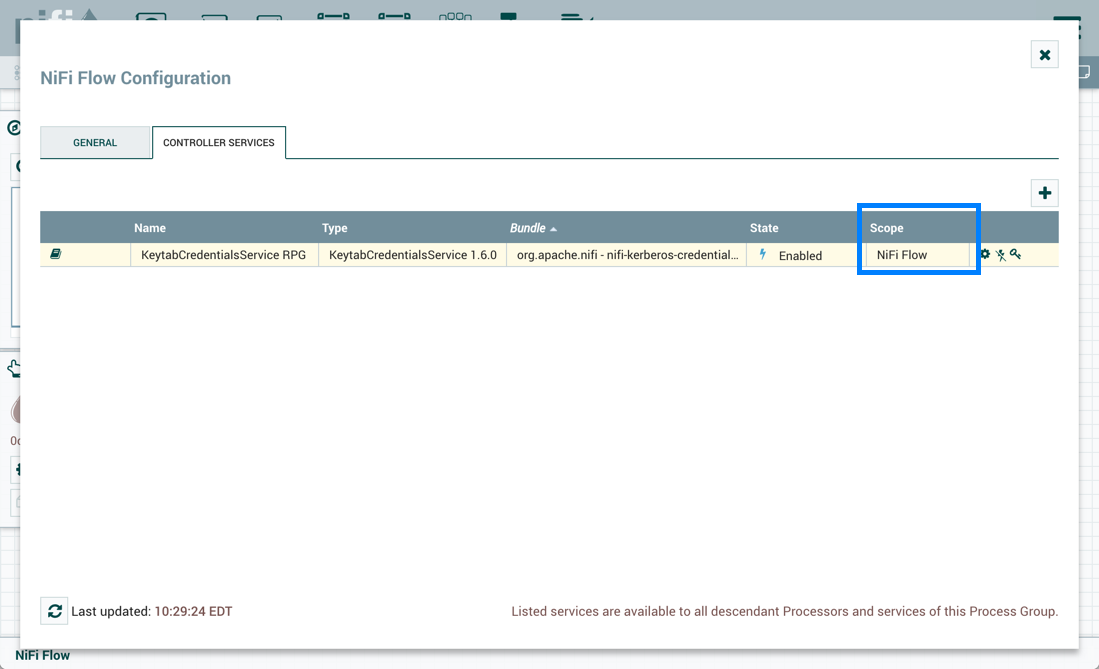
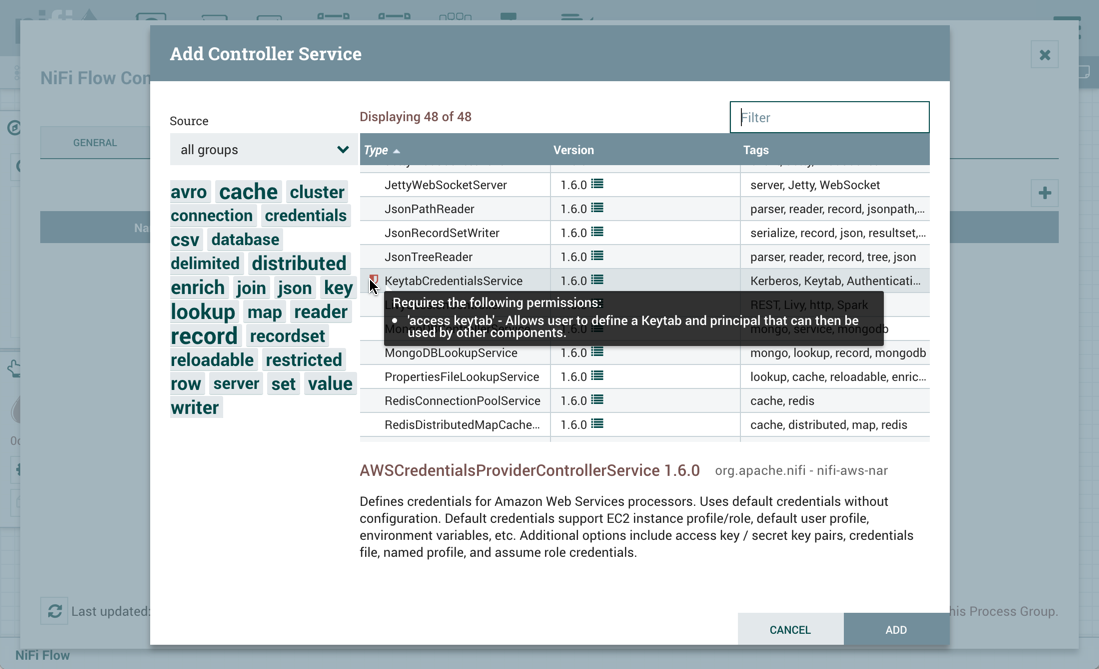
KeytabCredentialService controller service is a restricted component that requires 'access keytab' permissions:
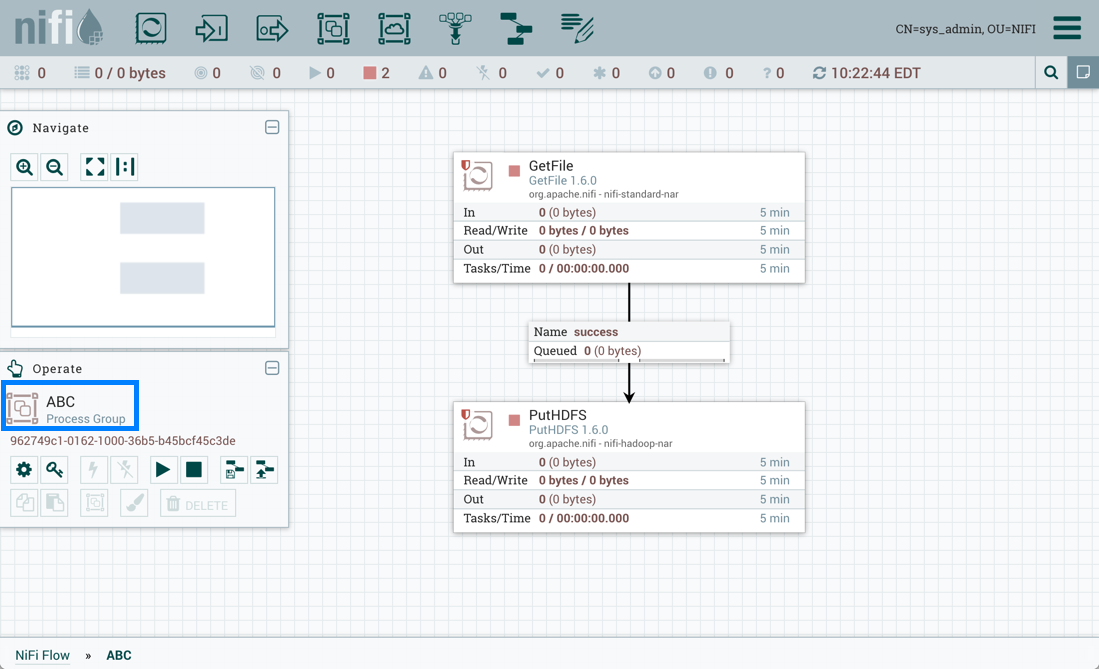
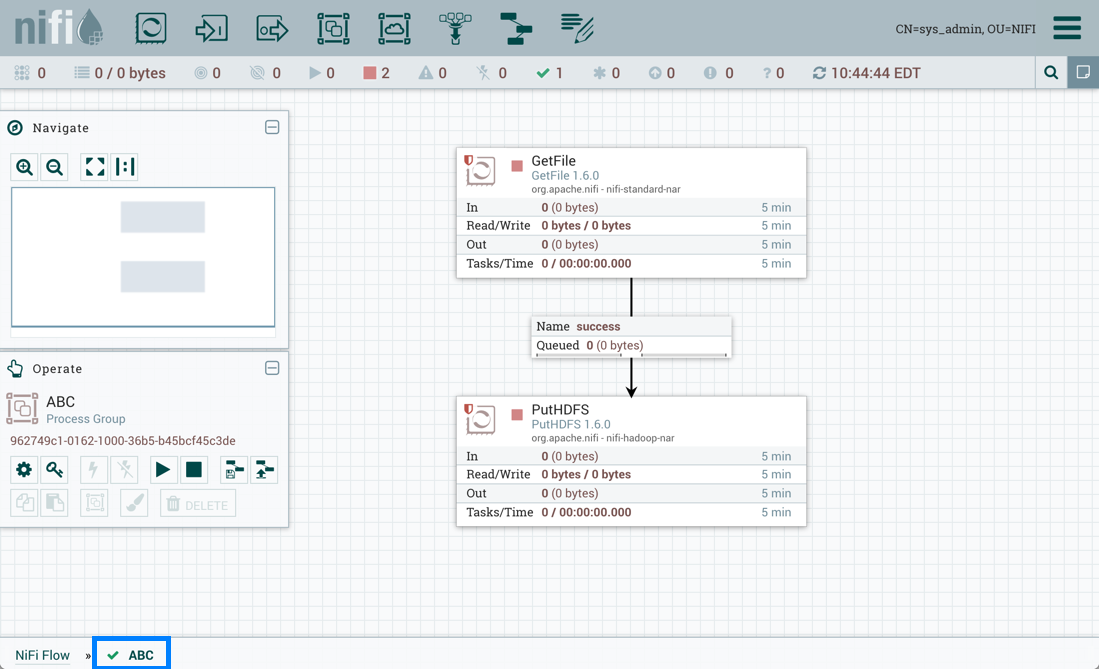
Sys_admin creates a process group ABC containing a flow with GetFile and PutHDFS processors:
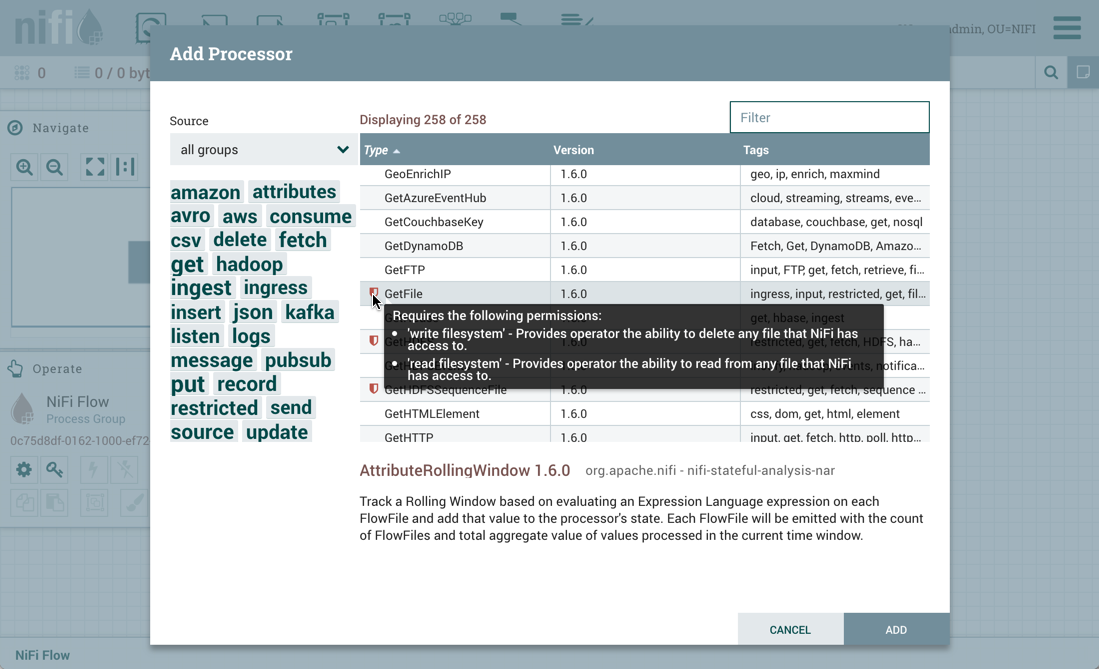
GetFile processor is a restricted component that requires 'write filesystem' and 'read filesystem' permissions:
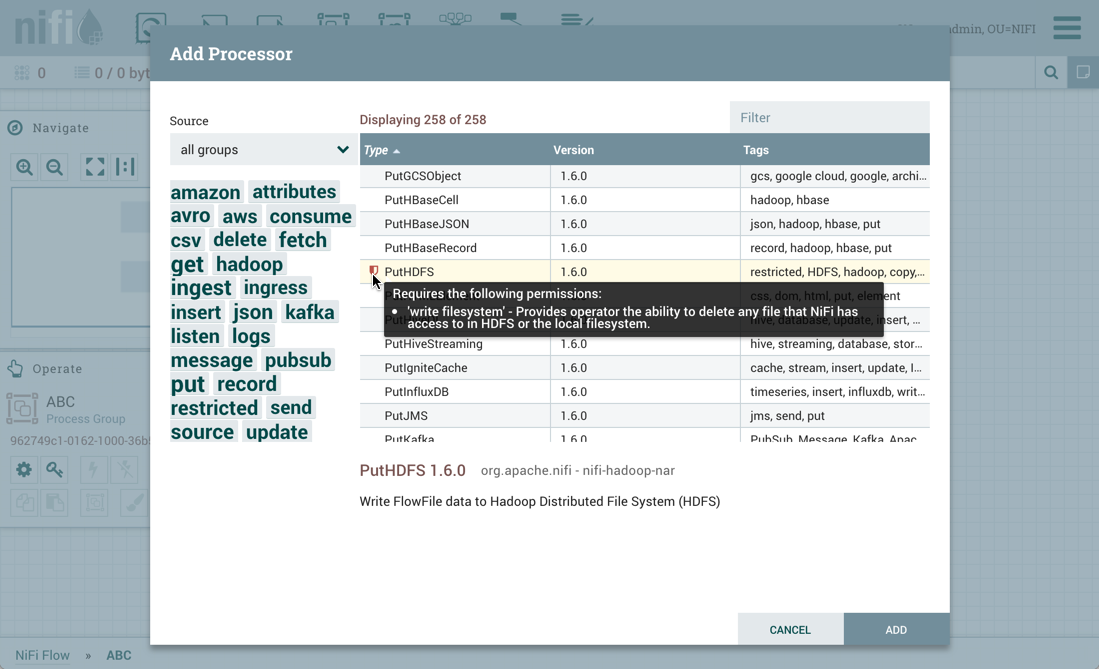
PutHDFS is a restricted component that requires 'write filesystem' permissions:
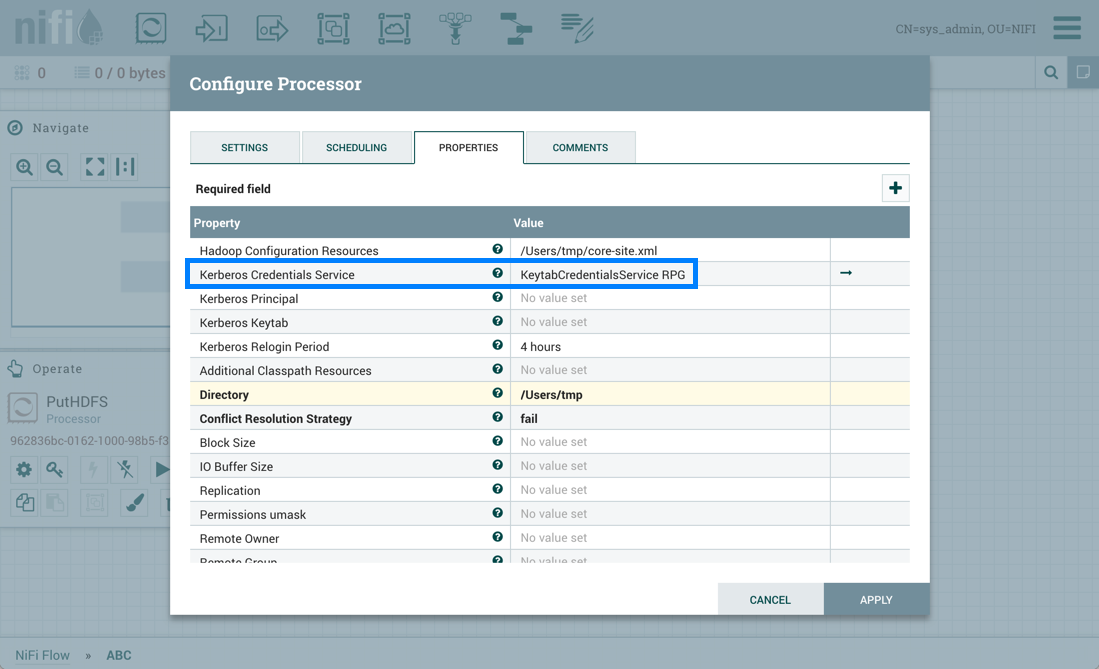
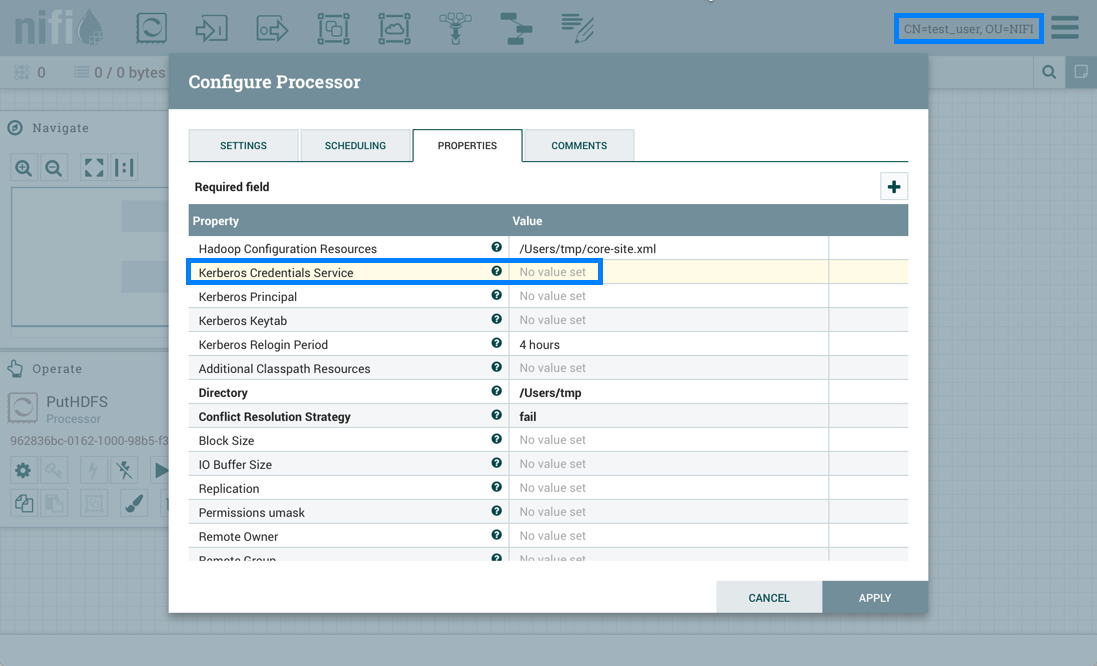
The PutHDFS processor is configured to use the root process group level KeytabCredentialsService controller service:
Sys_admin saves the process group as a versioned flow:
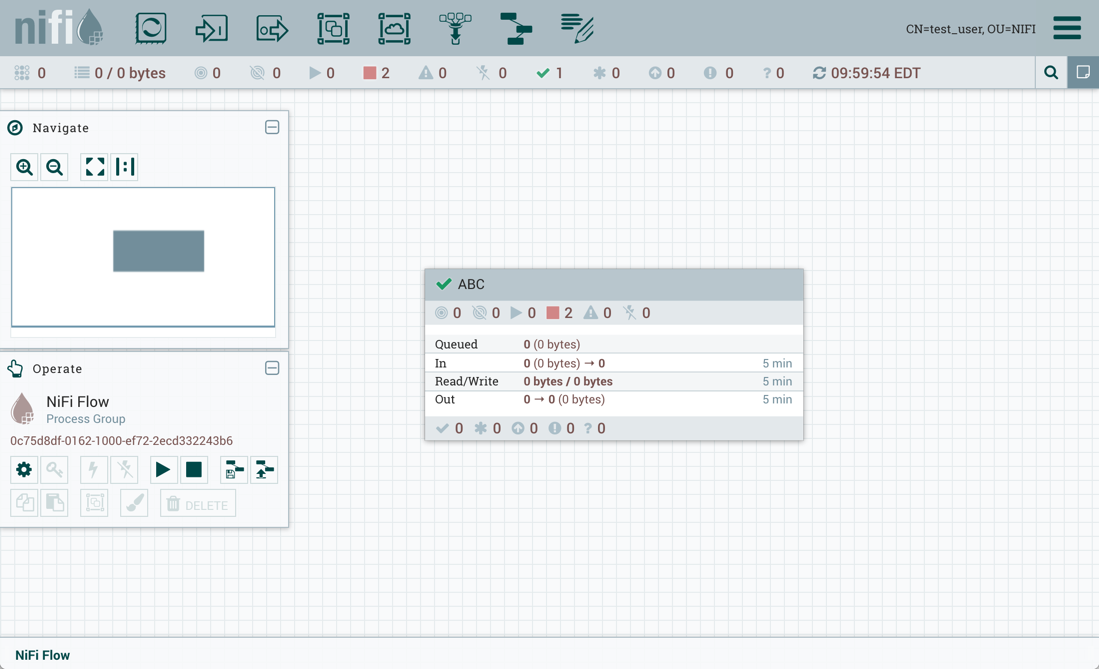
Test_user changes the flow by removing the KeytabCredentialsService controller service:
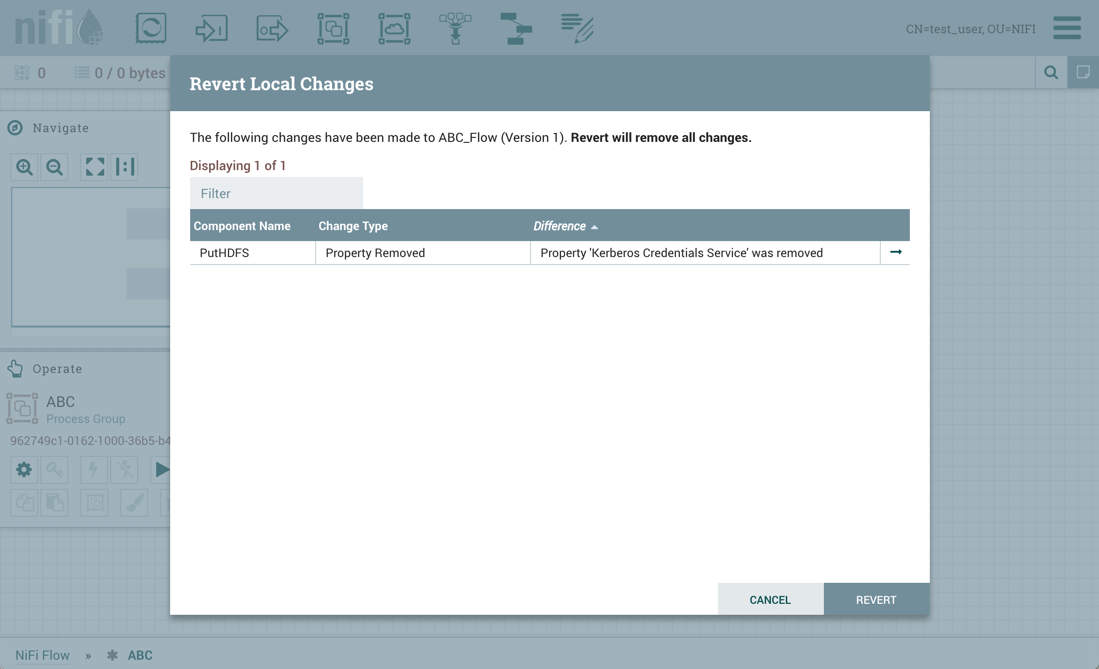
If test_user chooses to revert this change:
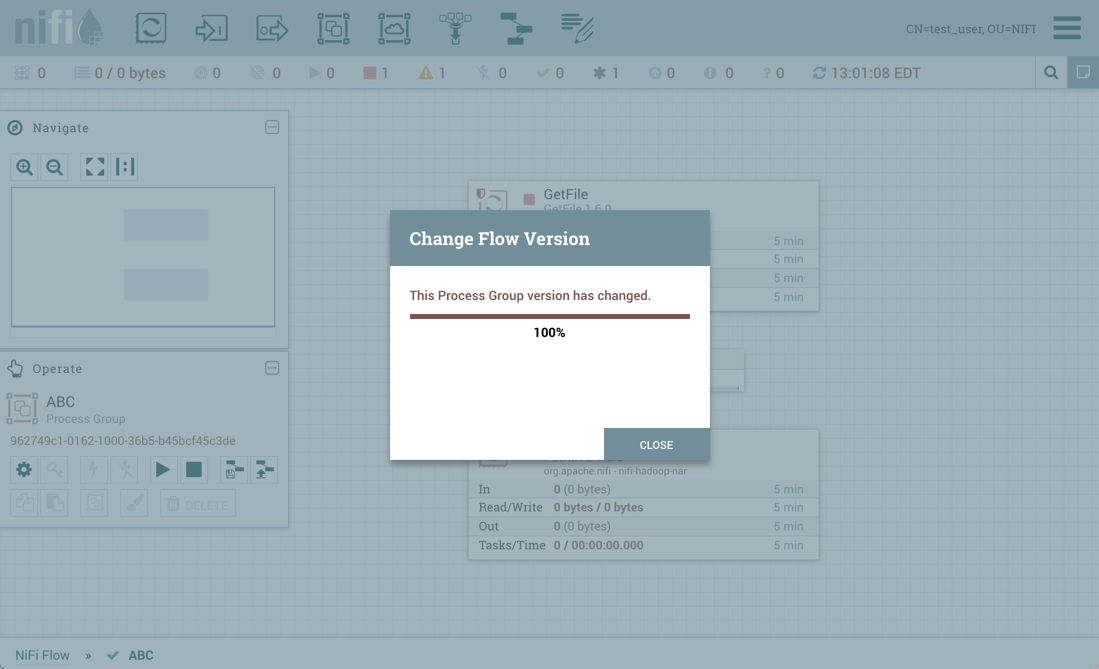
the revert is successful:
Additionally, if test_user chooses to import the ABC versioned flow:
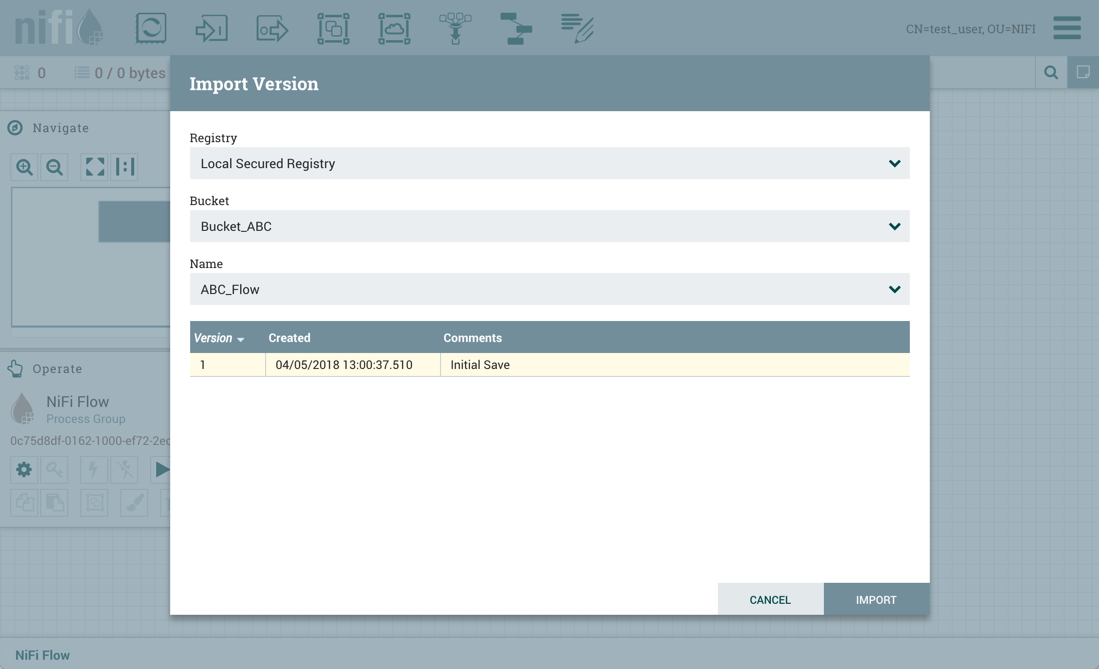
The import is successful: