Authenticating Hue users with Kerberos
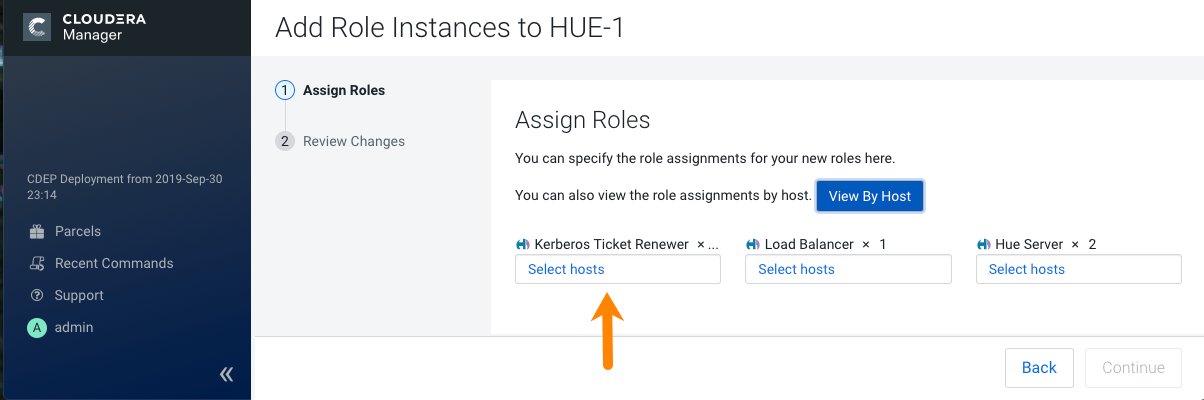
For Hue to work properly with a CDP cluster that uses Kerberos for authentication, the Kerberos Ticket Renewer role must be added to the Hue service.
Use the Cloudera Manager Admin Console to add the Kerberos Ticket
Renewer role to each host with a Hue Server role instance. The Hue Kerberos Ticket
Renewer renews only those tickets created for the Hue service principal:
hue/hostname@REALM-NAME. The Hue principal
impersonates other users for applications within Hue such as the Job Browser, File
Browser, and so on. Other services, such as HDFS and MapReduce, do not use the Hue
Kerberos Ticket Renewer. Instead these other services handle ticket renewal as needed by
using their own mechanisms.
Troubleshooting the Kerberos Ticket Renewer:
If the Hue Kerberos Ticket Renewer does not start, check the configuration of your
Kerberos Key Distribution Center (KDC). Look at the ticket renewal property,
maxrenewlife, to ensure that the principals,
hue/<host_name> and krbtgt,
are renewable. If these principals are not renewable, run the following commands on the
KDC to enable them:
kadmin.local: modprinc -maxrenewlife 90day krbtgt/<YOUR_REALM.COM>
kadmin.local: modprinc -maxrenewlife 90day +allow_renewable hue/<host_name>@<YOUR_REALM>