Configuring security for Storage Container Managers in High Availability
Configuring security and issuing certificates to Storage Container Managers (SCMs) along with Ozone Managers (OMs) and the DataNodes ensures secured communication in the Ozone cluster.
How the SCM issues certificates
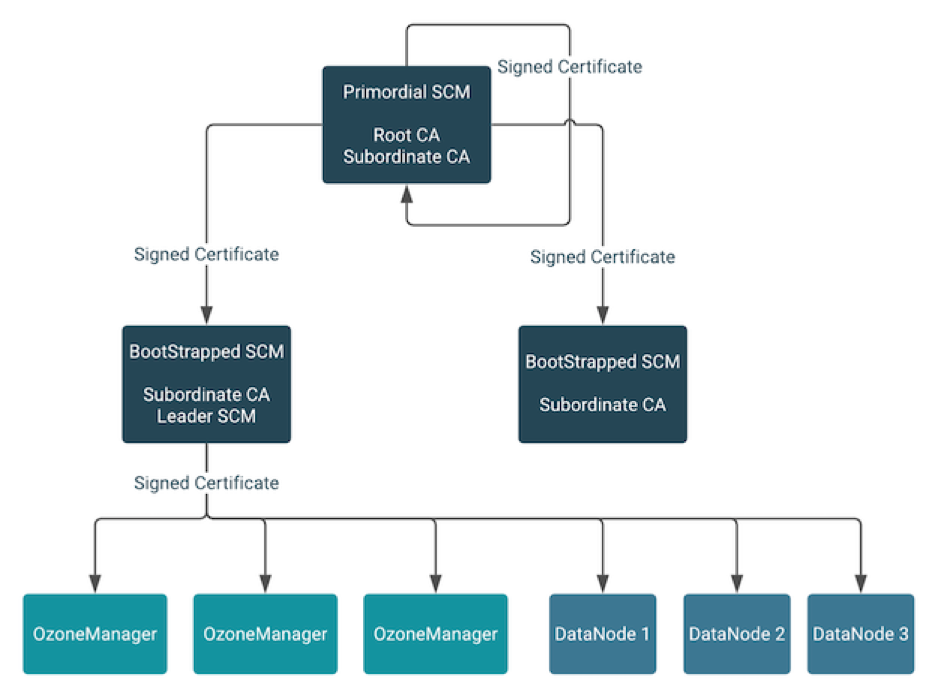
The primordial SCM in the HA configuration starts a root Certificate Authority (CA) with self-signed certificates. The primordial SCM issues signed certificates to itself and the other bootstrapped SCMs in the HA configuration. The primordial SCM also has a subordinate CA with a signed certificate from the root CA.
When an SCM is bootstrapped, it receives a signed certificate from the primordial SCM and starts a subordinate CA of its own. The subordinate CA of any SCM that becomes the leader in the HA configuration issues signed certificates to Ozone Managers and the DataNodes in the Ozone cluster.
How Ozone renews certificates
hdds.x509.default.duration), and
are automatically renewed once the certificate lifetime enters the renewal grace
period (hdds.x509.renew.grace.duration). This renewal process is
fully automated. It does not require any manual intervention or restart of the
service to take effect, as the certificates are applied automatically to any SSL
handshake happening after the renewal has happened, while the change in the
certificate does not affect any connections that are already established and remain
open even after the old certificate expires.