Introduction to Ranger RAZ in Cloudera Base on premises clusters
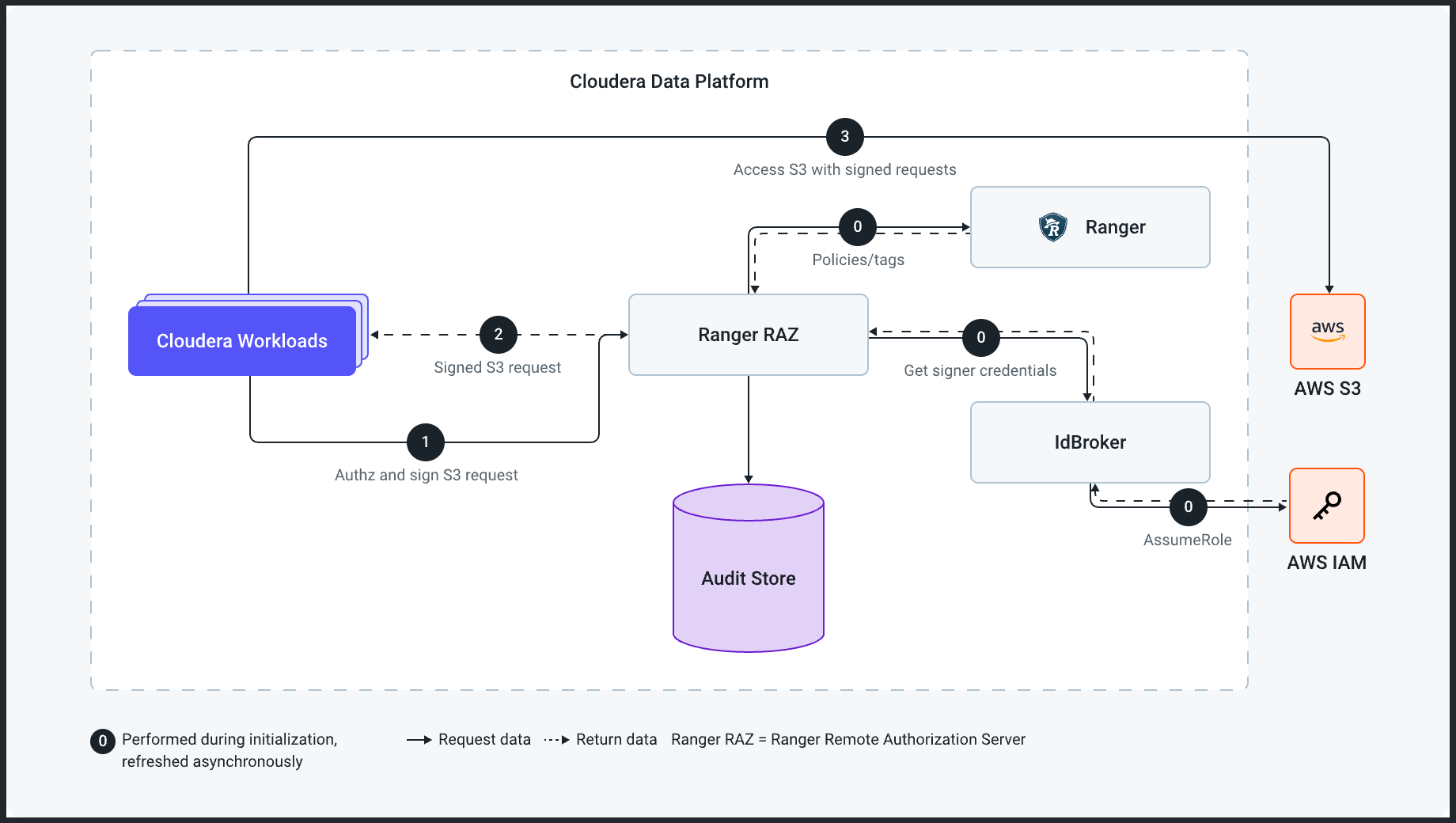
Learn how to support Amazon S3-compatible object stores through the Ranger Remote Authorization Service (RAZ).
Cloudera Base on premises defaults to HDFS and natively supports the Ozone object store. There was limited support for Amazon S3-compatible object stores with respect to executing workloads like Hive and Spark. Not all workloads were supported from an authorization perspective on Amazon S3-compatible object stores. The inconsistent policy framework created challenges for the Policy Administrator in terms of applying corporate policies to secure sensitive data. Managing data access across teams and individuals was an architectural challenge.
The Ranger RAZ resolves this challenge by using Apache Ranger policies to authorize access to Amazon S3-compatible object storage, similar to HDFS files.
- Hive or Impala executors
- Spark executors
- Data Explorer for accessing the users home and other accessible directories or transferring files.
- Per-user home directories.
- Data engineering (Spark) efforts that require access to cloud storage objects and directories.
- Data warehouse queries (Hive, Impala, or Iceberg) that use external tables.
- Access to Ranger's rich access control policies, such as date-based access revocation and user, group, or role-based controls, along with corresponding audits.
- Tag-based access control using the classification propagation feature that originates from directories.
