Configuring IAM role access for Iceberg replication
Iceberg replication in Data Lakes using AWS relies on AWS IAM role management. You must configure the required IAM role access for the Replication Manager users before you use or create Iceberg replication policies.
| IAM Role | Required Permissions |
|---|---|
| Source IAM role |
|
| Target IAM role |
|
-
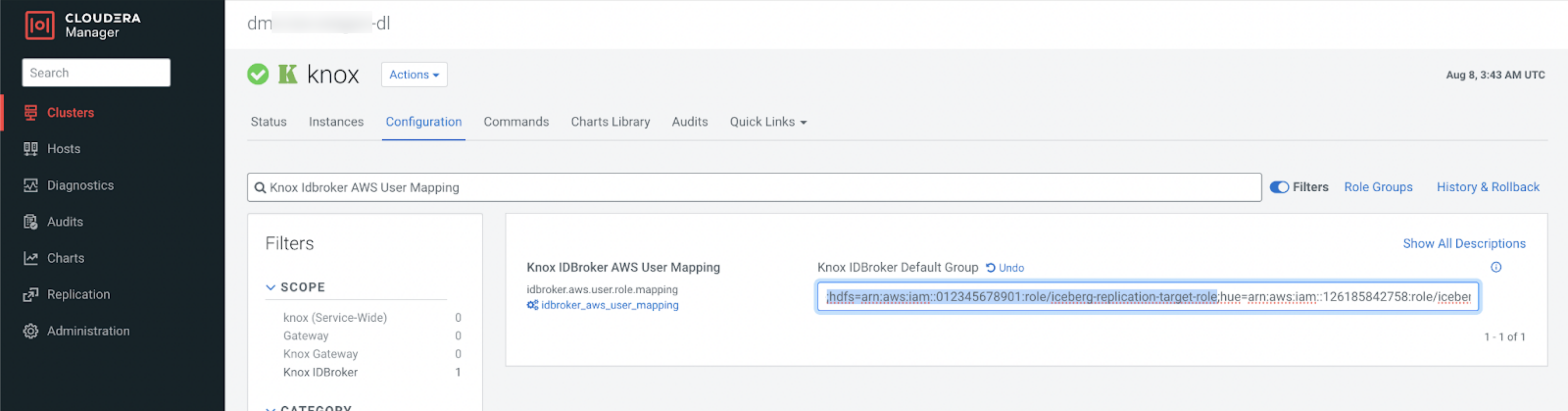
Verify whether the correct IAM role has been assigned and is available on the
source and target.
-
Configure the IAM role access in the AWS Console.