Cloudera Manager User Roles
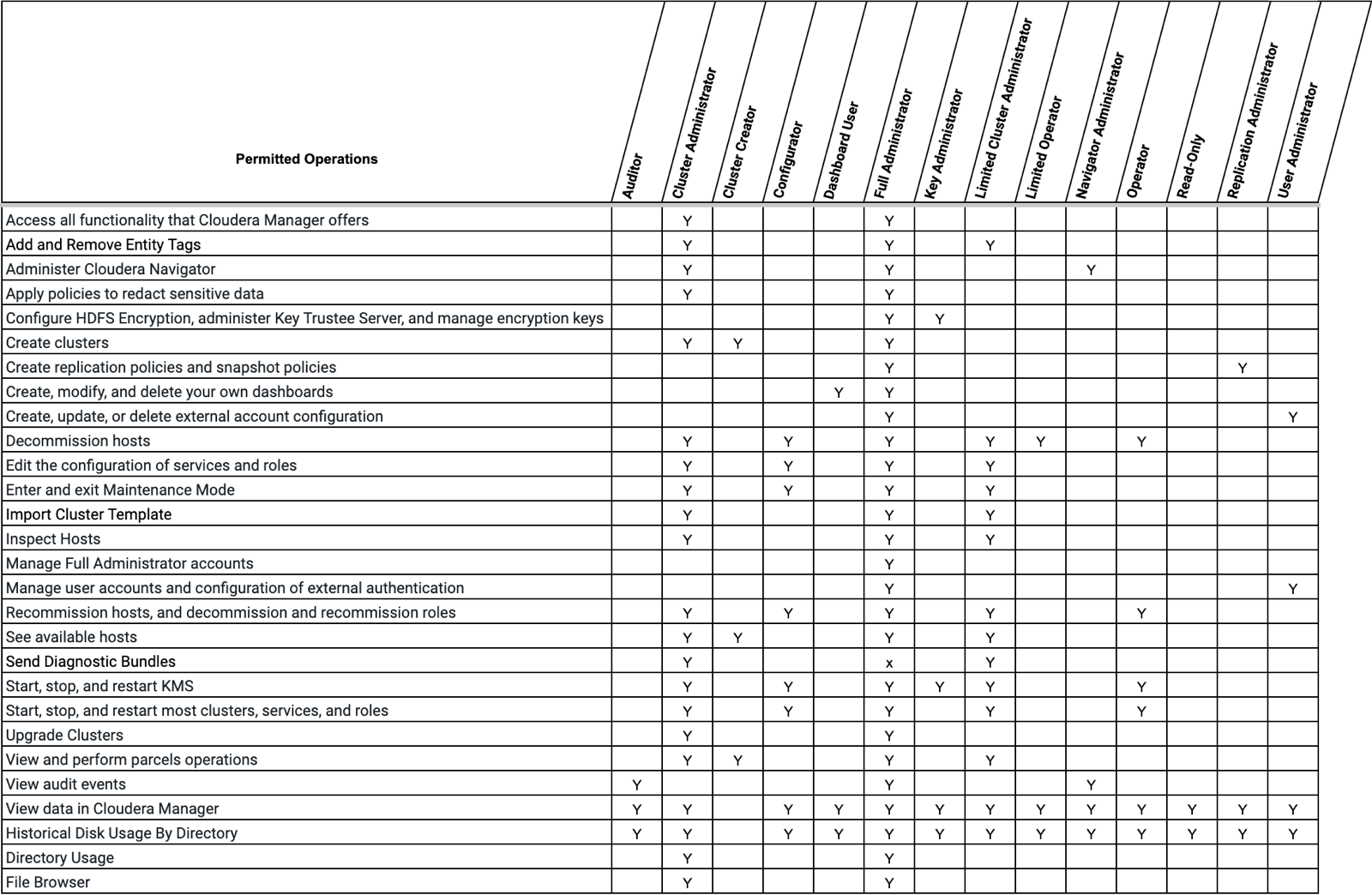
Access to Cloudera Manager features is controlled by user accounts that specify an authentication mechanism and one or more user roles
User roles determine the tasks that an authenticated user can perform and the features visible to the user in the Cloudera Manager Admin Console. In addition to the default user roles, you can create user roles that apply only to specific clusters.
Documentation for Cloudera Manager administration and management tasks indicate user roles required to perform the task.
Displaying Your Roles
To view your roles, perform the following step:
- In the Cloudera Manager Admin Console, select .
Default User Roles
By default, Cloudera Manager ships with user roles that have privileges for all clusters managed by Cloudera Manager. You can create roles that are a combination of a default user role and privileges on a specific cluster. For more information about this type of role, see User Roles with Privileges for a Cluster.
User Roles with Privileges for a Cluster
In addition to the default user roles, you can create user roles that apply only to specific clusters. Creating this new role is done by assigning a privilege for a specific cluster to a default role. When a user account has multiple roles, the privileges are the union of all the roles.
For example, the user account milton has the Limited
Operator role and Read-Only role with a scope of Cluster 1.
Additionally, milton has the Configurator role on
Cluster 2.
On Cluster 1, milton can perform all the actions that
a Limited Operator and Read-Only can.
On Cluster 2, milton can perform all the actions that
a Configurator can.
The user account milton cannot perform these or any
other actions on the other clusters that are managed by Cloudera Manager
because the account does not have any other roles.
Another user account, edith, has the Configurator role
with privileges for all clusters. This means that edith
can perform the actions of the Configurator role on all clusters that
Cloudera Manager manages since the scope is all clusters.
You can assign privileges for a specific cluster to the following user roles:
- Cluster Administrator
- Configurator
- Limited Operator
- Operator
- Read-Only
User roles that cannot be assigned privileges for a specific cluster
apply to all clusters. For example, if edith has the
Key Administrator user role, she can perform the actions of a Key
Administrator on all clusters.
Adding a User Role for a Specific Cluster
To create a role that has privileges for a specific cluster, perform the following steps:
- In the Cloudera Manager Admin Console, navigate to .
- Click Add Role.
- Specify the following:
- Privilege: The user role and cluster you want to assign privileges for.
- Users: The users you want to assign to this new role. You can assign users now or at a later time.
- LDAP Group/External Program Exit Codes/SAML
Attributes/SAML Script Exit Codes: The external
mapping you want to assign this new role to. You can assign
external mappings now or at a later time with the process
described in Mapping External Authentication to a Role.
This field is based on your authentication mode and does not appear for local users.
Valid values for the External Program Exit Code and SAML Script Exit Code are between 0 and 127. You defined what users you want to associate with theses values when you configure your external authentication. For more information,
If you are upgrading to Cloudera Manager 6 from Cloudera Manager 5, existing mappings are imported from Cloudera Manager 5. These imported mappings can be changed.
The following list describes the LDAP groups imported from Cloudera Manager 5:
- LDAP Full Administrator Groups
- LDAP User Administrator Groups
- LDAP Cluster Administrator Groups
- LDAP BDR Administrator Groups
- LDAP Configurator Groups
- LDAP Key Administrator Groups
- LDAP Navigator Administrator Groups
- LDAP Operator Groups
- LDAP Limited Operator Groups
- LDAP Auditor Groups
The following list describes the SAML and External Program codes imported from Cloudera Manager 5:
- 0 - Full Administrator
- 1 - Read-Only
- 2 - Limited Operator
- 3 - Operator
- 4 - Configurator
- 5 - Cluster Administrator
- 6 - BDR Administrator
- 7 - Navigator Administrator
- 8 - User Administrator
- 9 - Auditor
- 10 - Key Administrator
- 11 - Dashboard User
- Click Add.
Mapping External Authentication to a Role
For example, you are using a SAML Script and want to assign user
accounts that correspond with exit code 15 to a Cluster Administrator
role with privileges for a cluster named cluster1.
To accomplish this, perform the following steps in the Cloudera Manager Admin Console:
- Navigate to .
- Based on your authentication method, select LDAP Groups, SAML Attributes, SAML Scripts, or External Programs.
- Click Add <authentication method> Mapping.
- Fill in the value for your authentication method, such as SAML
Script Exit Code, and select the role you want to map to that value
from the dropdown menu.
For SAML Scripts and External Programs, valid values are between 0 and 127.
- Click Save.
- Repeat this process for all the roles you want to map.
If you are upgrading to Cloudera Manager 6 from Cloudera Manager 5, existing mappings are imported from Cloudera Manager 5. These imported mappings can be changed.
The following list describes the LDAP groups imported from Cloudera Manager 5:
- LDAP Full Administrator Groups
- LDAP User Administrator Groups
- LDAP Cluster Administrator Groups
- LDAP BDR Administrator Groups
- LDAP Configurator Groups
- LDAP Key Administrator Groups
- LDAP Navigator Administrator Groups
- LDAP Operator Groups
- LDAP Limited Operator Groups
- LDAP Auditor Groups
The following list describes the SAML and External Program codes imported from Cloudera Manager 5:
- 0 - Full Administrator
- 1 - Read-Only
- 2 - Limited Operator
- 3 - Operator
- 4 - Configurator
- 5 - Cluster Administrator
- 6 - BDR Administrator
- 7 - Navigator Administrator
- 8 - User Administrator
- 9 - Auditor
- 10 - Key Administrator
- 11 - Dashboard User
Assigning Users to a Role
In addition to mapping groups, such as LDAP groups, to a user role, you can also assign individual users to a user role. If you do not assign a role, the local user defaults to no access. This means that the user cannot perform any actions on the cluster.
To add a user account to a role, perform the following steps:
- In the Cloudera Manager Admin Console, navigate to .
- Click Assign for the role you want to modify.
- Specify the Users or <Authentication Method Value> groups you want to assign to the role.
- Save the changes.
Removing a User or External Mapping from a User Role
Perform the following steps to remove a user account or external mapping from a user role:
- In the Cloudera Manager Admin Console, navigate to .
- Click Assign for the role you want to modify.
- Click the X for each user or external mapping you want to remove from the user role and click Save.
Removing a Role
To remove a role with a specific privilege, you must first remove all the user accounts that have that role. Note that you cannot remove the default roles that Cloudera Manager ships with.
- In the Cloudera Manager Admin Console, navigate to .
- Click Assign for the role you want to modify.
- Click the X for each user or external mapping you want to remove from the user role and click Save.
- Click Remove.
Removing the Full Administrator User Role
Minimum Required Role: User Administrator (also provided by Full Administrator) This feature is not available when using Cloudera Manager to manage Data Hub clusters.
In some organizations, security policies may prohibit the use of the Full Administrator role. The Full Administrator role is created during Cloudera Manager installation, but you can remove it as long as you have at least one remaining user account with User Administrator privileges.
To remove the Full Administrator user role, perform the following steps.
- Add at least one user account with User Administrator privileges, or ensure that at least one such user account already exists.
- Ensure that there is only a single user account with Full Administrator privileges.
- While logged in as the single remaining Full Administrator user, select your own user account and either delete it or assign it a new user role.
- If the machine that the Cloudera Navigator roles are running on needs to be replaced, the Cluster Administrator will want to move all the roles running on that machine to a different machine. The Cluster Administrator can move any non-Navigator roles by deleting and re-adding them, but would need a Navigator Administrator to perform the stop, delete, add, and start actions for the Cloudera Navigator roles.
- In order to take HDFS snapshots, snapshots must be enabled on the cluster by a Cluster Administrator, but the snapshots themselves must be taken by a BDR Administrator.
