Setting up certificates for Cloudera AI Inference Service
Cloudera AI Inference service requires its own dedicated TLS certificate as it operates through a separate Istio gateway that does not support shared certificates.
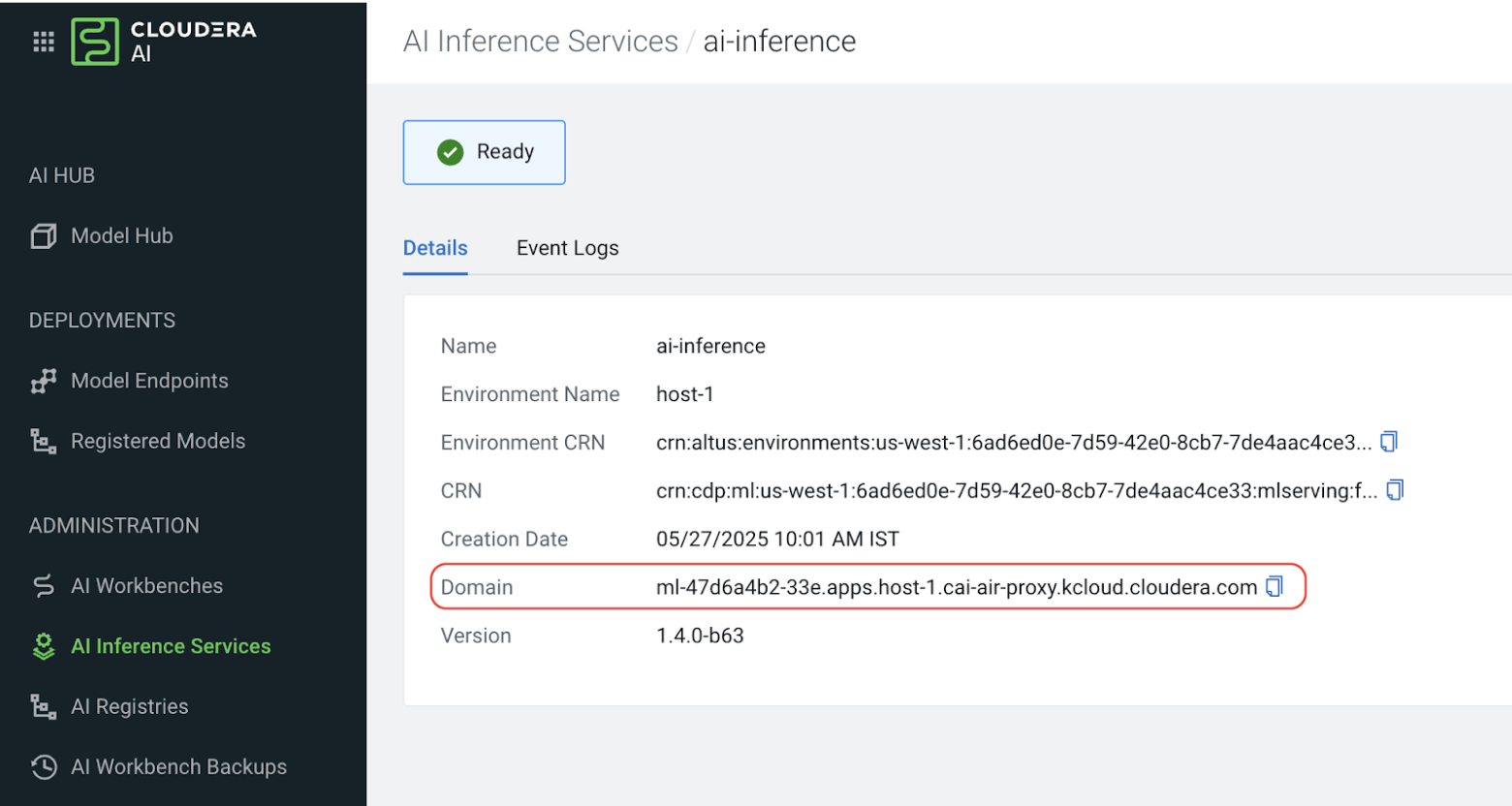
After successfully installing the Cloudera AI Inference service follow these steps to update the certificates for Cloudera AI Inference service.