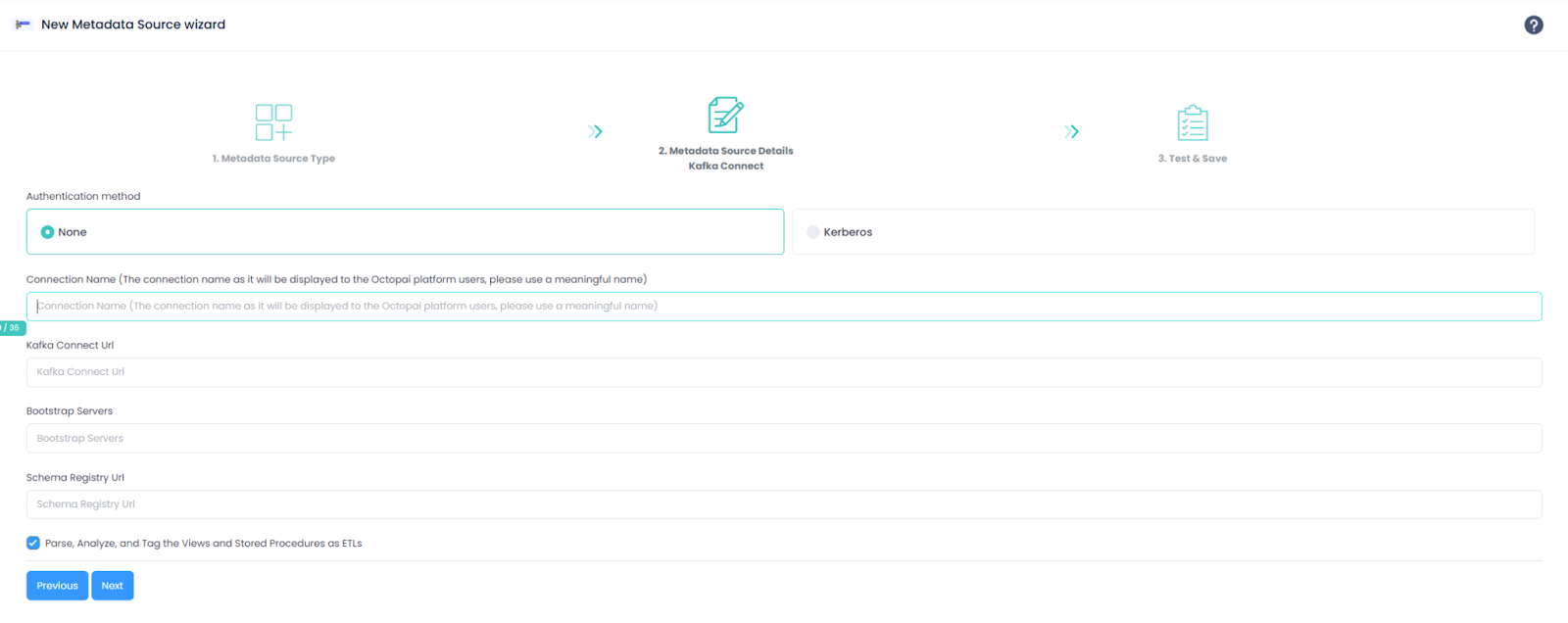
Configuring Kafka and Kafka Connect Connector in Cloudera Octopai
Learn how to configure Kafka and Kafka Connect connector in Cloudera Octopai Client using Kerberos authentication (SASL/GSSAPI).
Before configuring Kafka and Kafka Connect connectors in Cloudera Octopai Client, ensure the following components are available and properly configured:
- Kerberos infrastructure: Active Kerberos Key Distribution Center (KDC), valid Kerberos realm configuration, and network connectivity from the Octopai Client host to the KDC.
- MIT Kerberos for Windows: Install MIT Kerberos
for Windows on the machine running Cloudera Octopai
Client. The default installation path is C:\Program
Files\MIT\Kerberos\bin\kinit.exe. Cloudera Octopai Client uses
kinitto acquire Kerberos tickets. - Kerberos configuration file: The Kerberos
configuration file must exist at
C:\ProgramData\MIT\Kerberos5\krb5.ini.
Example configuration:
[libdefaults] default_realm = ROOT.COMOPS.SITE dns_lookup_realm = false dns_lookup_kdc = false ticket_lifetime = 24h renew_lifetime = 7d forwardable = true [realms] ROOT.COMOPS.SITE = { kdc = ccycloud-1.cdp.root.comops.site admin_server = ccycloud-1.cdp.root.comops.site } [domain_realm] .root.comops.site = ROOT.COMOPS.SITE root.comops.site = ROOT.COMOPS.SITE - Kerberos credentials: Obtain a Kerberos
principal (for example,
kafka-user@REALM) and its associated keytab file (for example, C:\octopai\kafka-user.keytab). Ensure the keytab file is securely stored and accessible. - Kafka cluster configuration: Ensure the Kafka
cluster is configured with SASL/GSSAPI enabled, the Kafka service principal is
configured on the brokers (for example,
kafka/hostname@REALM), and the broker hostnames are resolvable using fully qualified domain names.
Kerberos authentication errors:
- Verify the principal format:
username@REALM - Confirm the keytab path and permissions.
- Validate the realm configuration in krb5.ini
Kafka connectivity issues:
- Verify the network connectivity.
- Use fully qualified domain names.
- Confirm the SASL listener configuration.
Ticket expiration:
- Verify the
ticket_lifetimeandrenew_lifetimevalues. - Adjust the renewal configuration, if required.
Clock skew:
Synchronize the system time:
w32tm /resync /forceError during the extraction:
- Collect the logs from C:\Program Files
(x86)\Octopai\Service\log
- Send the logs with the connector number and name to Cloudera Support.