Authentication with Apache Knox
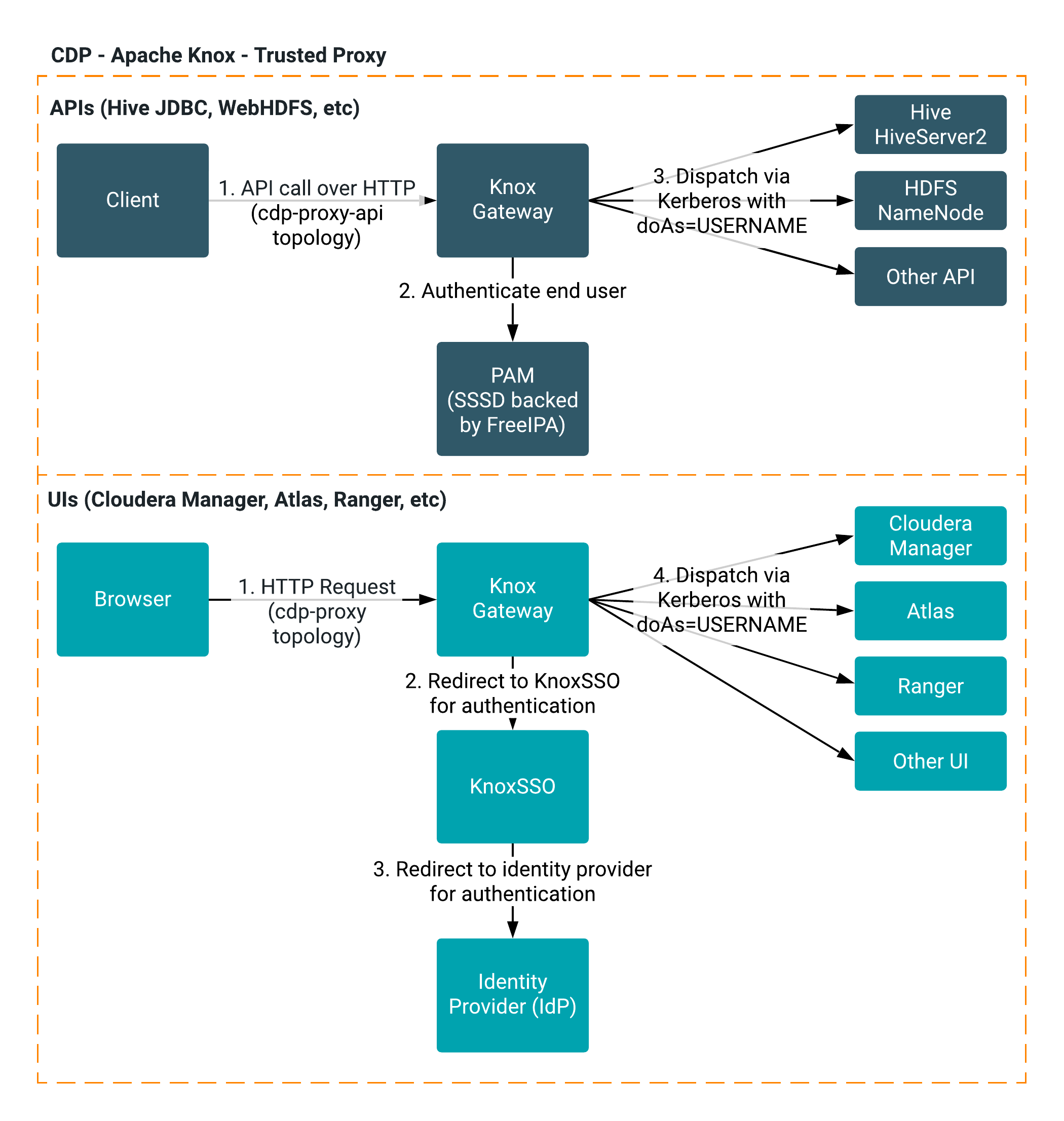
Apache Knox handles proxy for web UIs and APIs, and Trusted Proxy propagates the authenticated end user to the backend service.
Knox Gateway
Apache Knox Gateway is a reverse proxy that authenticates and provides a single access point for REST and HTTP interactions with the CDP Data Hub clusters.
Trusted proxy
Knox Trusted Proxy is useful in cloud deployments when you need the seamless and uniform authentication benefits of both proxy and SSO. Trusted Proxy is automatically configured by Cloudera Manager in CDP deployments.
Knox Trusted Proxy propagates the authenticated end user to the backend service. The request is "trusted" in that the given backend/service is able to validate that the request came from a certain place and was allowed to make the request. A backend in this case is any service that Knox is acting as a proxy for (e.g., Cloudera Manager, Hive JDBC, Ranger UI, etc). Each of these services have a mechanism to ensure that the 1) request IP address and 2) request user matches what it expects. If the request matches those two things, then the service will not have to authenticate again and can trust that Knox sent the request.
When making requests to the cluster, Knox first authenticates the end user, and then
adds that user as a query parameter to the request (?doAs=USERNAME) to the
backend. The backend then checks that the request is trusted (request IP and request user) and
extracts the end user (USERNAME) from the query parameter. The backend service
then does whatever is necessary as that backend user. Knox and the proxied services authenticate
to each other via Kerberos.
SSO via Knox
Knox SSO is configured automatically.
