Performing Threat Triage Using the Management Module
To create a threat triage rule configuration, you must first define your rules. These rules identify the conditions in the data source data flow and associate alert scores with those conditions.
Before you can prioritize a threat intelligence enrichment, you must ensure that the enrichment is working properly.
Following are some example rules with example values:
- Rule 1
If a threat intelligence enrichment type is alerted, you receive an alert score of 5.
- Rule 2
If the URL does not end in .com or .net, you receive an alert score of 10.
To create similar rules, complete the following steps:
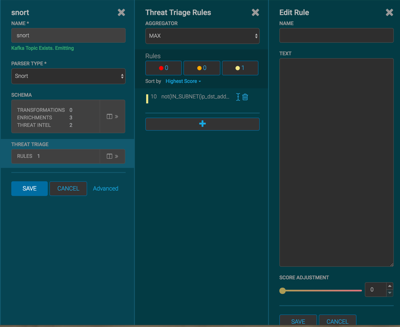
On the sensor panel, in the Threat Triage field, click

To add a rule, click .
Assign a name to the new rule in the NAME field.
In the TEXT field, enter the syntax for the new rule:
Exists(IsAlert)
Use the SCORE ADJUSTMENT slider to choose the threat score for the rule.
Click
The new rule is listed in the Threat Triage Rules panel.
Choose how you want to aggregate your rules by choosing a value from the Aggregator menu.
You can choose among the following:
- MAX
The maximum of all of the associated values for matching queries.
- MIN
The minimum of all of the associated values for matching queries.
- MEAN
The mean of all of the associated values for matching queries.
- POSITIVE_MEAN
The mean of the positive associated values for the matching queries.
If you want to filter the threat triage display, use the Rules section and the Sort by menu below it.
For example, to display only high-levels alerts, click the box containing the red indicator. To sort the high-level alerts from highest to lowest, select Highest Score from the Sort by menu.
Click SAVE.