Parse the Squid Telemetry Event
The following procedures use the Management UI whenever possible. If you would like to
see these steps performed using the CLI, see the HCP Administration Guide.
Parsers transform raw data into JSON messages suitable for downstream enrichment and indexing by HCP. There is one parser for each data source and HCP pipes the information to the Enrichment/Threat Intelligence topology. You can transform the field output in the JSON messages into information and formats that make the output more useful. For example, you can change the timestamp field output from GMT to your timezone.
-
Launch the Management UI:
-
From the Ambari Dashboard panel, click Metron.
Make sure you have the Summary tab selected.
-
Select Management UI from Quick
Links.
The Management UI tool should display in a separate browser tab.
-
From the Ambari Dashboard panel, click Metron.
- Click Sensors on the left side of the window, under Operations.
-
Click
 (add button) in the lower right corner of the screen.
The Management UI displays a panel used to create the new sensor.
(add button) in the lower right corner of the screen.
The Management UI displays a panel used to create the new sensor.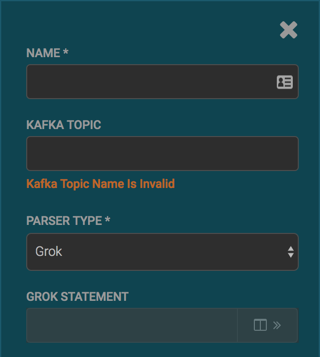
-
Enter the following information:
Name: mysquid Kafka Topic: mysquid Parser Type: GrokIf a Kafka topic already exists for the sensor name, the UI displays a message similar to Kafka Topic Exists. Emitting and displays the name of the Parser Type. You can skip to the next section, Verify Events are Indexed. -
Create a Grok statement for the new parser:
-
In the Grok Statement box, click the
 (expand window) to display the Grok
Validator panel.
(expand window) to display the Grok
Validator panel.
-
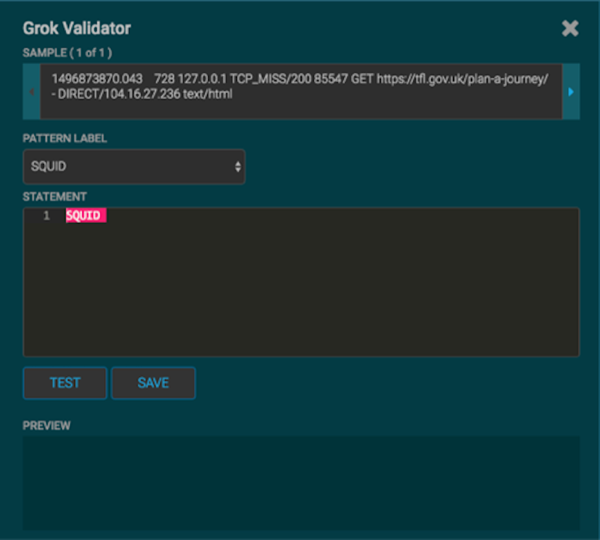
Choose or enter a name for the Grok statement in the PATTERN
LABEL field.
For our example, we chose MYSQUID.
-
Enter a sample log entry for the data source.
To create sample log entries, see Step 15 in Create a NiFi Flow to Stream Events to HCP.
-
Refer to the format of the log entries you determined in Step 11d in
Create a NiFi Flow to Stream Events to HCP.
For example, the log entry format for Squid is:
timestamp | time elapsed | remotehost | code/status | bytes | method | URL rfc931 peerstatus/peerhost | type -
In the STATEMENT field, enter the first element in the
sensor log file.
For Squid, the first element in the sensor log file is
timestampwhich is a number, so we enter%{NUMBER:timestamp}. NoteThe Management UI automatically completes partial words in your Grok statement as you enter them.
NoteThe Management UI automatically completes partial words in your Grok statement as you enter them.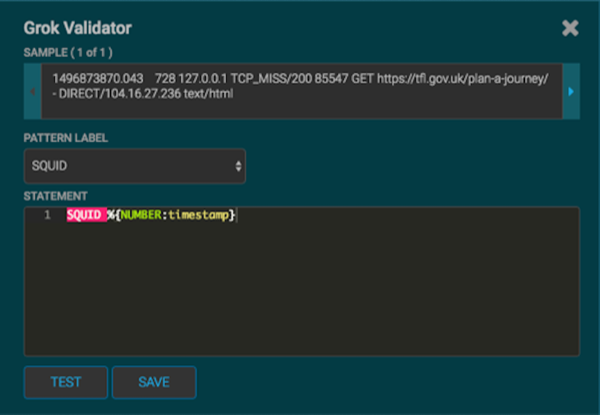
-
Click TEST.
If the validator finds an error, it displays the error information. If the validation succeeds, it displays the valid mapping in the PREVIEW field.Because you entered the timestamp element, the validator parses the timestamp correctly and leaves the rest of the information as random data.

- Click Save.
- Verify that the sensor name and topic name are "mysquid" with NO extra spaces or special characters.
-
In the Grok Statement box, click the
-
Click Save on the mysquid sensor.
The mysquid sensor appears in the Management UI. You might need to refresh your screen to see the new sensor.
- Click the pencil icon to edit the mysquid sensor.
- Scroll down to the Parser Config section.
-
In the first open field, indicated by enter field, enter
timestampField.
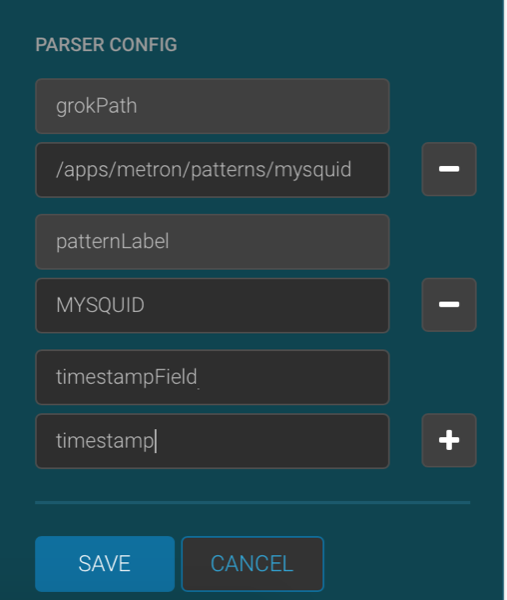
- In next open field, enter timestamp.
- Click Save.
-
Continue to build and test the Grok statement until you have entries for each
element in the log entry.
For example, for Squid, the second element is
elapsed, so we enter%{INT:elapsed}and click TEST again.
- When your Grok statement is complete and valid, click SAVE to save the Grok statement for the sensor.
-
Click SAVE to save the sensor information and add it to the
list of Sensors.
This new data source processor topology ingests from the $Kafka topic and then parses the event with the HCP Grok framework using the Grok pattern. The result is a standard JSON Metron structure that then is added to the "enrichment" Kafka topic for further processing.
-
Test that a Kafka topic has been created for the Squid parser:
-
Navigate to the following directory:
/usr/hdp/current/kafka-broker/bin -
List all of the Kafka topics:
./kafka-topics.sh --zookeeper localhost:2181 --listYou should see the following list of Kafka topics:- bro
- enrichments
- ubdexubg
- snort
- mysquid
-
Navigate to the following directory:

