Choosing manual TLS or Auto-TLS
An explanation of the difference between manual TLS and Auto-TLS in Cloudera Manager.
Wire encryption protects data in motion, and Transport Layer Security (TLS) is the most widely used security protocol for wire encryption. TLS provides authentication, privacy and data integrity between applications communicating over a network by encrypting the packets transmitted between endpoints. Users interact with Hadoop clusters via browser or command line tools, while applications use REST APIs or Thrift.
Overview of enabling TLS manually
The typical process to enable wire encryption on Cloudera Data Platform Private Cloud clusters is described below.
- Generate a public/private keypair on each host
- Generate the Certificate signing request (CSR) for all the hosts.
- Get the CSR signed by the company’s internal Certificate Authority (CA).
- Generate keystore & truststore and deploy them across all the cluster hosts.
- For each service, enable TLS by setting the keystore and truststore configuration.
- Restart the affected components before proceeding to enable TLS for the next service.
- Make the required changes outside of the cluster manager’s UI (like setting up truststore, Enabling Knox SSL, etc.)
- For new service installation, the keystore and truststore information need to be configured for the service. Restart the impacted services.
- For each new host to be added to the cluster, admins would have to perform the steps from the “Get Certificates” section (only for the new hosts).
- The certificates are rotated before they expire.
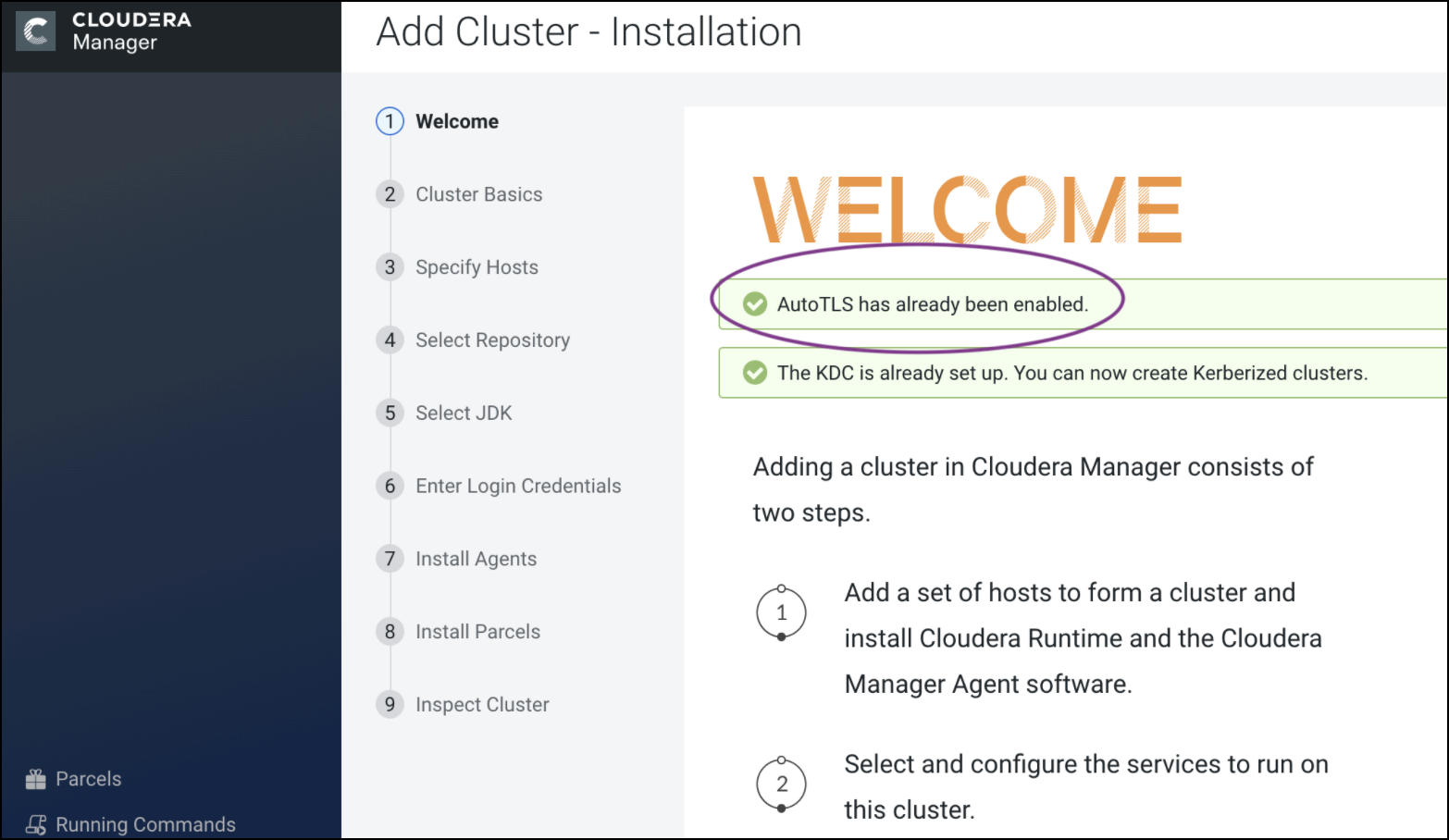
Auto-TLS feature in Cloudera Manager
The process described above can be a significant effort in large deployments, often leading to long deployment times and operational difficulties. The Auto-TLS feature automates all the steps required to enable TLS encryption at a cluster level. Using Auto-TLS, you can let Cloudera manage the Certificate Authority (CA) for all the certificates in the cluster or use the company’s existing CA. In most cases, all the necessary steps can be enabled easily via the Cloudera Manager UI. This feature automates the following processes –
- Creates the root Certificate Authority or a Certificate Signing Request (CSR) for creating an intermediate Certificate Authority to be signed by company’s existing Certificate Authority (CA)
- Generates the CSRs for hosts and signs them automatically
- Creates a keystore and truststore for hosts.
- Deploys the certificates, keystore and truststore to all the hosts in the cluster.
- All the cluster services are then automatically TLS enabled by configuring the keystore and truststore information from a role instance specific directory.
- Enables TLS for Cloudera Manager server and agents.
- After this initial setup, any new service, hosts (or) additional compute clusters setup are automatically TLS enabled by default.
- Provides an automation framework for rotating certificates.
- Use case 1: Using Cloudera Manager to generate an internal CA and corresponding certificates
- Use case 2: Enabling Auto-TLS with an existing Root CA
- Use case 3: Enabling Auto-TLS with existing Certificates
New Cluster deployment
Summary
The Auto-TLS functionality not only speeds up the initial setup of the wire encryption but also automates future TLS configuration steps for the cluster. The following table summarizes the differences between the options described in this blog.
| Steps | HDP/EDH (manual) | CDP Private Cloud use case 1 - Using Cloudera Manager to generate an internal CA and corresponding certificates | CDP Private Cloud use case 2 - Enabling Auto-TLS with an existing Root CA | CDP Private Cloud use case 3 - Enabling Auto-TLS with Existing Certificates |
|---|---|---|---|---|
| Generate CSR | Manual | Automated | Automated | Manual |
| CSR Signed by CA | Manual | Automated | One-time | Manual |
| Deploy certificate to all hosts | Manual | Automated | Automated | Automated |
| Configuration for each service | Manual | Automated | Automated | Automated |
| Cluster restarts | Multiple | Once | Once | Once |
| Configuration steps | Manual | Automated | Automated | Automated |
| New Service steps | Manual | Automated | Automated | Automated |
| New Host cert. generation | Manual | Automated | Automated | Manual |
