Installing CDP Private Cloud Data Services using ECS
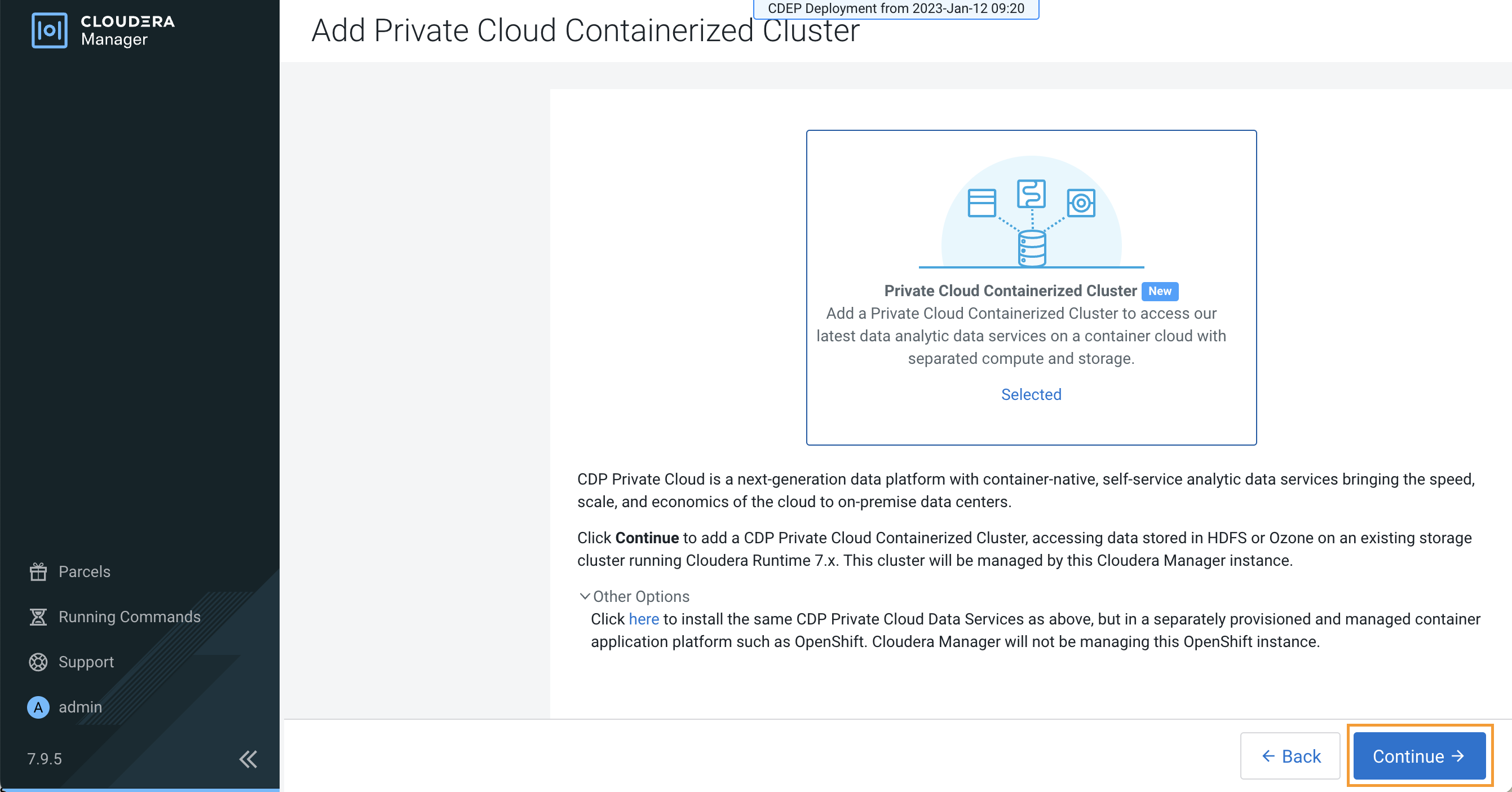
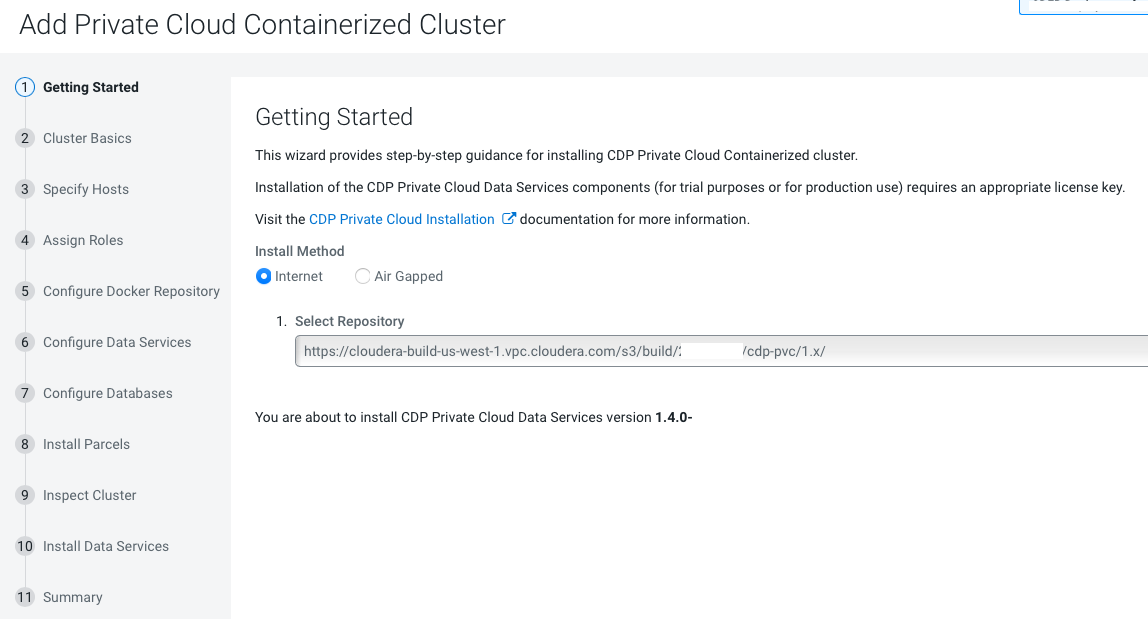
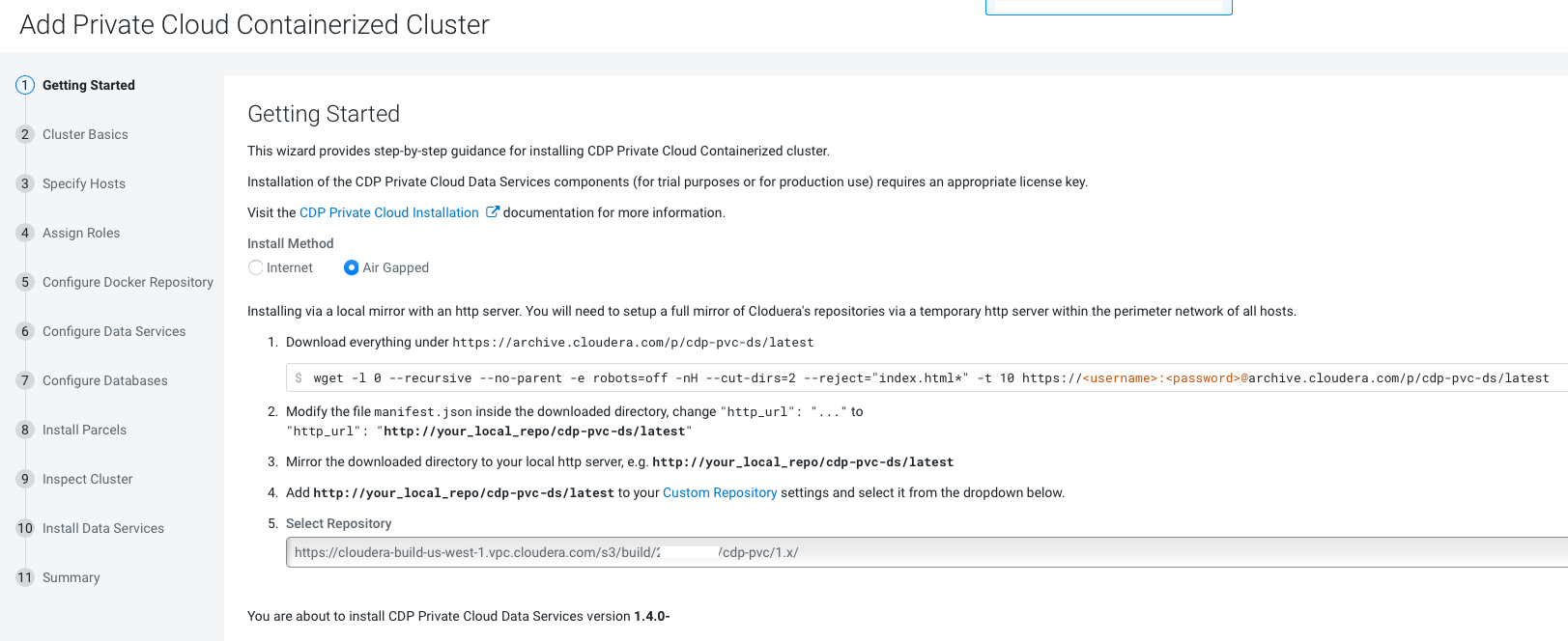
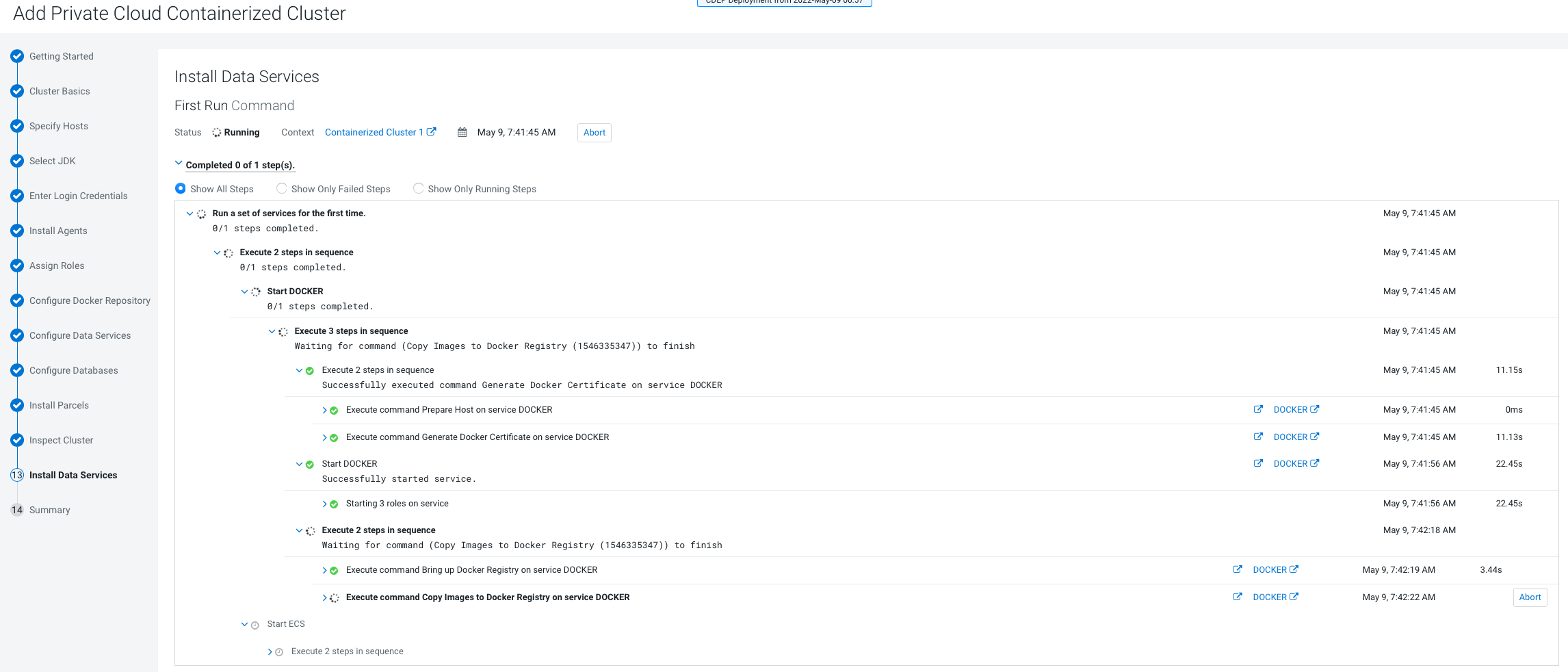
Follow the steps in this topic to install CDP Private Cloud Data Services with the Embedded Container Service (ECS).
If the installation fails, and you see the following error message in the stderr output during the Install Longhorn UI step, retry the installation by clicking the Resume button.
++ openssl passwd -stdin -apr1 + echo 'cm-longhorn:$apr1$gp2nrbtq$1KYPGI0QNlFJ2lo5sV62l0' + kubectl -n longhorn-system create secret generic basic-auth --from-file=auth + rm -f auth + kubectl -n longhorn-system apply -f /opt/cloudera/cm-agent/service/ecs/longhorn-ingress.yaml Error from server (InternalError): error when creating "/opt/cloudera/cm-agent/service/ecs/longhorn-ingress.yaml":
Internal error occurred: failed calling webhook "validate.nginx.ingress.kubernetes.io": Post "https://rke2-ingress-nginx-controller-admission.kube-system.svc:443/networking/v1/ingresses?timeout=10s": x509: certificate signed by unknown authority
- If you specified a custom certificate, select the ECS cluster in Cloudera
Manager, then select Actions > Update Ingress Controller.
This command copies the
cert.pemandkey.pemfiles from the Cloudera Manager server host to the ECS Management Console host. - Click Open Private Cloud Data Services to launch your CDP Private Cloud Data Services instance.
- Log in using the default username and password admin.
- On the Welcome to CDP Private Cloud page, click Change Password to change the Local Administrator Account password.
- Set up external authentication using the URL of the LDAP server and a CA certificate of your secure LDAP. Follow the instructions on the Welcome to CDP Private Cloud page to complete this step.
- Click Test Connection to ensure that you are able to connect to the configured LDAP server.
- Create your first Virtual Warehouse in the CDW Data Service
- Provision an ML Workspace in the CML Data Service
- Add a CDE service in the CDE Data Service