Cloudera Private Links Network for AWS
Cloudera Private Links Network enables you to connect privately and securely to the Cloudera Control Plane without traversing the internet. You can use Cloudera Private Links Network for end-to-end encryption of your workloads between Cloudera Control Plane and AWS VPC endpoints.
- High-level options of VPC endpoint placement
- Configuration options and other considerations for DNS overrides
- Cloudera Private Links Network deployment process
- Instructions of how to set up both Private Link options:
- VPC: Setup of Cloudera Private Links Network for a workload VPC through CDP CLI
- Authorization: Authorization with CDP CLI to enable the setup of Cloudera Private Links Network through your automation tools
- References for proxy profile configuration and considerations, and Cloudera Private Links Network commands
Comparison of connectivity setup without and with Cloudera Private Links Network


With Cloudera Private Links Network, the Cloudera Control Plane is accessed as if the Cloudera Control Plane would be on your network. This means that IP addresses are assigned to the Cloudera Control Plane services from your network, and DNS lookups will return your local IP addresses.
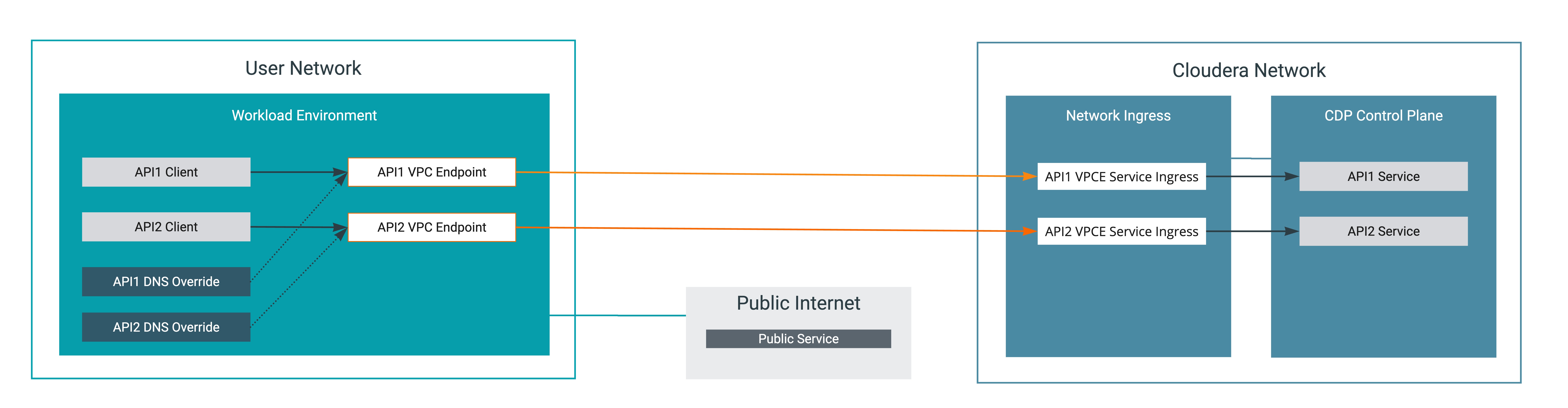
The following options are available for DNS overrides:
- DNS is a per-VPC view: Deploying a VPC endpoint with private DNS option enabled will automatically install the DNS overrides in the local VPC.
- DNS is a regional or global view: Installing overrides at a regional or global scope will impact DNS resolution for other VPCs, other VPCs will attempt to use the VPC endpoints of the local VPC.
This section does not include an exhaustive list of design options, but should cover most cases. For more information about more advanced use cases, see the Additional VPC scenarios section.
Cloudera Private Links Network creates an additional layer of security with Private Links and security groups with inbound rule. If security groups are already present in your network, they will be updated with an inbound rule for safe HTTPs traffic. As inbound rules are created or updated within setting up the Cloudera Private Links Network, outbound rules can be removed.
DNS overrides
The DNS hostnames for Cloudera services remain the same, whether the services are accessed through the internet or through VPC endpoints. DNS resolution in the customer networks perform DNS lookups against the public internet. Responses will contain the public internet IP addresses for the Cloudera services. DNS override records must be set up in your DNS infrastructure, and the hostnames need to be repointed to the VPC endpoint or IP addresses. For more information, see Setting up DNS overrides.
Multi-region support
The AWS multi-region support for Private Links enables you to connect your VPC in one region to a VPC endpoint service in a different region.
- US Cloudera Control Plane:
us-west-2 - EU Cloudera Control Plane:
eu-central-1 - AP Cloudera Control Plane:
ap-southeast-2
ca-central-1 region, and
requested a Private Link connection for the Cluster Connectivity Manager service in the
US Cloudera Control Plane, as Cluster Connectivity Manager is supported in
the us-west-2 region, and not in ca-central-1, the connection
is established using the us-west-2 region.For more information about the AWS inter-region support, see Introducing Cross-Region Connectivity for AWS PrivateLink.
