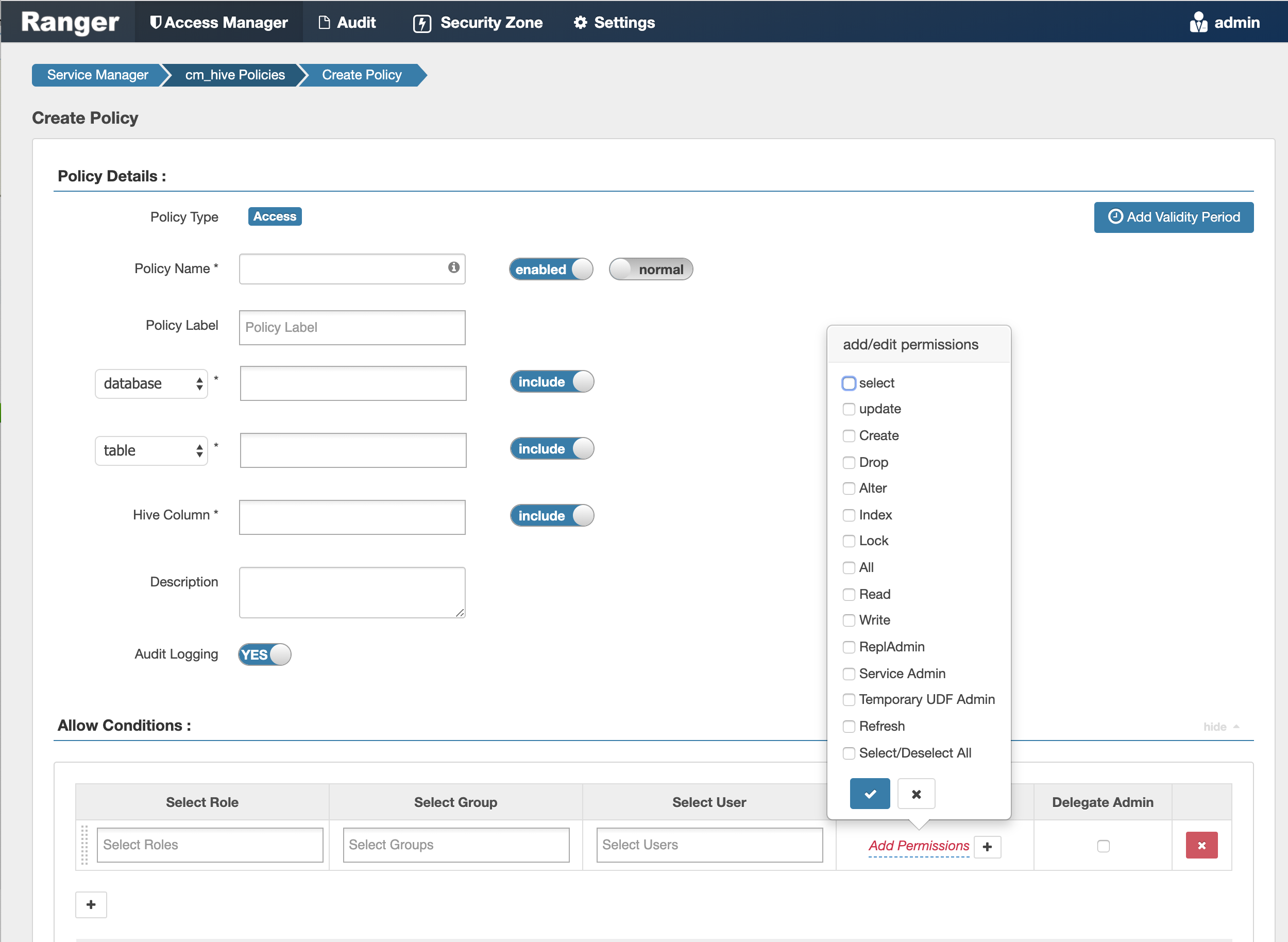
Configure a resource-based policy: Hive
How to add a new policy to an existing Hive service.
-
On the Service Manager page, select an existing Hive service.
The List of Policies page appears.
-
Click Add New Policy.
The Create Policy page appears.
-
Complete the Create Policy page as follows:
Table 1. Policy Details Field Description Policy Name Enter an appropriate policy name. This name cannot be duplicated across the system. This field is mandatory. The policy is enabled by default. normal/override Enables you to specify an override policy. When override is selected, the access permissions in the policy override the access permissions in existing policies. This feature can be used with Add Validity Period to create temporary access policies that override existing policies. Database Type in the applicable database name. The autocomplete feature displays available databases based on the entered text.
Include is selected by default to allow access. Select Exclude to deny access..
table/udf Specifies a table-based or UDF-based policy.
Select table or udf, then type in the applicable table or UDF name. The autocomplete feature displays available tables based on the entered text.
Include is selected by default to allow access. Select Exclude to deny access.
Hive Column Type in the applicable Hive column name. The autocomplete feature displays available columns based on the entered text.
Include is selected by default to allow access. Select Exclude to deny access.
URL Specify the cloud storage path (for example
s3a://dev-admin/demo/campaigns.txt) where the end-user permission is needed to read/write the Hive data from/to a cloud storage path.Permissions: READ operation on the URL permits the user to perform HiveServer2 operations which use S3 as data source for Hive tables. WRITE operation on the URL permits the user to perform HiveServer2 operations which write data to the specified S3 location.
This feature is a Technical Preview: it is not ready for production deployment.
URI Hive INSERT OVERWRITE queries require a Ranger URI policy to allow write operations, even if the user has write privilege granted through HDFS policy.
Failure to specify this field will result in the following error:
Error while compiling statement: FAILED: HiveAccessControlException Permission denied: user [jdoe] does not have [WRITE] privilege on [/tmp/*] (state=42000,code=40000)Example value: /tmp/*
Description (Optional) Describe the purpose of the policy.
Hive Service Name hiveservice is used only in conjunction with Permissions=Service Admin. Enables a user who has Service Admin permission in Ranger to run the kill query API: kill query <queryID>. Supported value:*. (Required)Audit Logging Specify whether this policy is audited. (De-select to disable auditing). Policy Label Specify a label for this policy. You can search reports and filter policies based on these labels. Add Validity Period Specify a start and end time for the policy. Table 2. Allow Conditions Label
Description
Select Role Specify the roles to which this policy applies. To designate a role as an Administrator, select the Delegate Admin check box. Administrators can edit or delete the policy, and can also create child policies based on the original policy.
Select Group Specify the groups to which this policy applies.
To designate a group as an Administrator, select the Delegate Admin check box. Administrators can edit or delete the policy, and can also create child policies based on the original policy.
The public group contains all users, so granting access to the public group grants access to all users.
Select User Specify the users to which this policy applies.
To designate a user as an Administrator, select the Delegate Admin check box. Administrators can edit or delete the policy, and can also create child policies based on the original policy.
Permissions Add or edit permissions: Select, Update, Create, Drop, Alter, Index, Lock, All, ReplAdmin, Service Admin, Select/Deselect All.
Service Admin is used in conjunction with Hive Service Name and the kill query API:
kill query <queryID>.Delegate Admin You can use Delegate Admin to assign administrator privileges to the roles, groups, or users specified in the policy. Administrators can edit or delete the policy, and can also create child policies based on the original policy. - You can use the Plus (+) symbol to add additional conditions. Conditions are evaluated in the order listed in the policy. The condition at the top of the list is applied first, then the second, then the third, and so on.
- You can use Deny All Other Accesses to deny access to all other users, groups, and roles other than those specified in the allow conditions for the policy.
- Click Add.
Provide User Access to Hive Database Tables from the Command Line
Hive provides the means to manage user access to Hive database tables directly from the command line. The most commonly-used commands are:
-
GRANT
Syntax:
grant <permissions> on table <table> to user <user or group>;For example, to create a policy that grants user1 SELECT permission on the table default-hivesmoke22074, the command would be:
grant select on table default.hivesmoke22074 to user user1;The syntax is the same for granting UPDATE, CREATE, DROP, ALTER, INDEX, LOCK, ALL, and ADMIN rights.
-
REVOKE
Syntax:
revoke <permissions> on table <table> from user <user or group>;For example, to revoke the SELECT rights of user1 to the table default.hivesmoke22074, the command would be:
revoke select on table default.hivesmoke22074 from user user1;The syntax is the same for revoking UPDATE, CREATE, DROP, ALTER, INDEX, LOCK, ALL, and ADMIN rights.
