Setting up Knox SSO for Apache Atlas
This section describes how to configure Apache Atlas to use Knox SSO (Single Sign-on) to authenticate users on an Ambari cluster. With this configuration, unauthenticated users who try to access Atlas are redirected to the Knox SSO login page for authentication.
![[Note]](../common/images/admon/note.png) | Note |
|---|---|
|
Use the following steps to configure Knox SSO for Atlas:
Install Ambari with HDP-2.6 or higher. Install Knox along with the other services.
The Knox SSO topology settings are preconfigured in Knox > Configs > Advanced knoxsso-topology.
Run the following CLI command to export the Knox certificate:
JAVA_HOME/bin/keytool -export -alias gateway-identity -rfc -file knox-pub-key.cert -keystore /usr/hdp/current/knox-server/data/security/keystores/gateway.jks
When prompted, enter the Knox master password.
Note the location where you save the
cert.pemfile.
Select Atlas > Configs > Authentication.
Select the Enable Knox SSO check box, then set the following properties:
atlas.sso.knox.providerurl – Enter the Knox SSO Provider URL:
https://<knox_host>:8443/gateway/knoxsso/api/v1/webssoatlas.sso.knox.publicKey – Paste in the contents of the
cert.pemcertificate file exported from Knox, excluding the header and footer.atlas.sso.knox.browser.useragent – Enter the browsers to use with Knox SSO, for example:
Mozilla,chrome
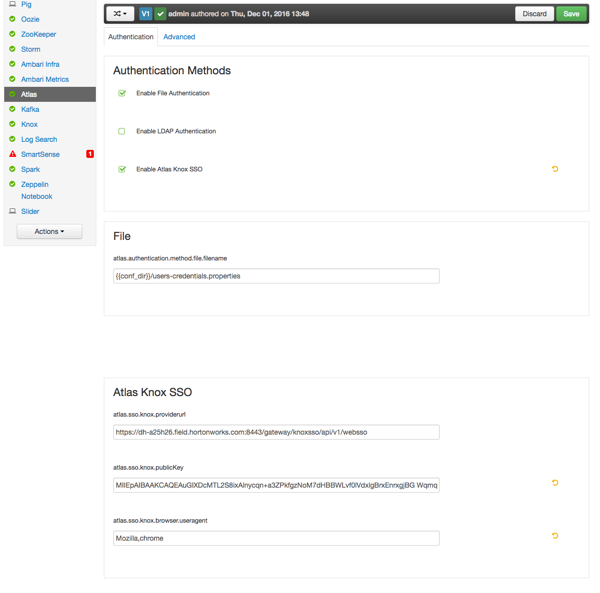
[D]Click Save to save the new configuration, then click through the confirmation pop-ups.
Restart Atlas. Select Actions > Restart All Required to restart all other services that require a restart.
Knox SSO should now be enabled. Users who try to access Atlas are redirected to the Knox SSO login page for authentication.

