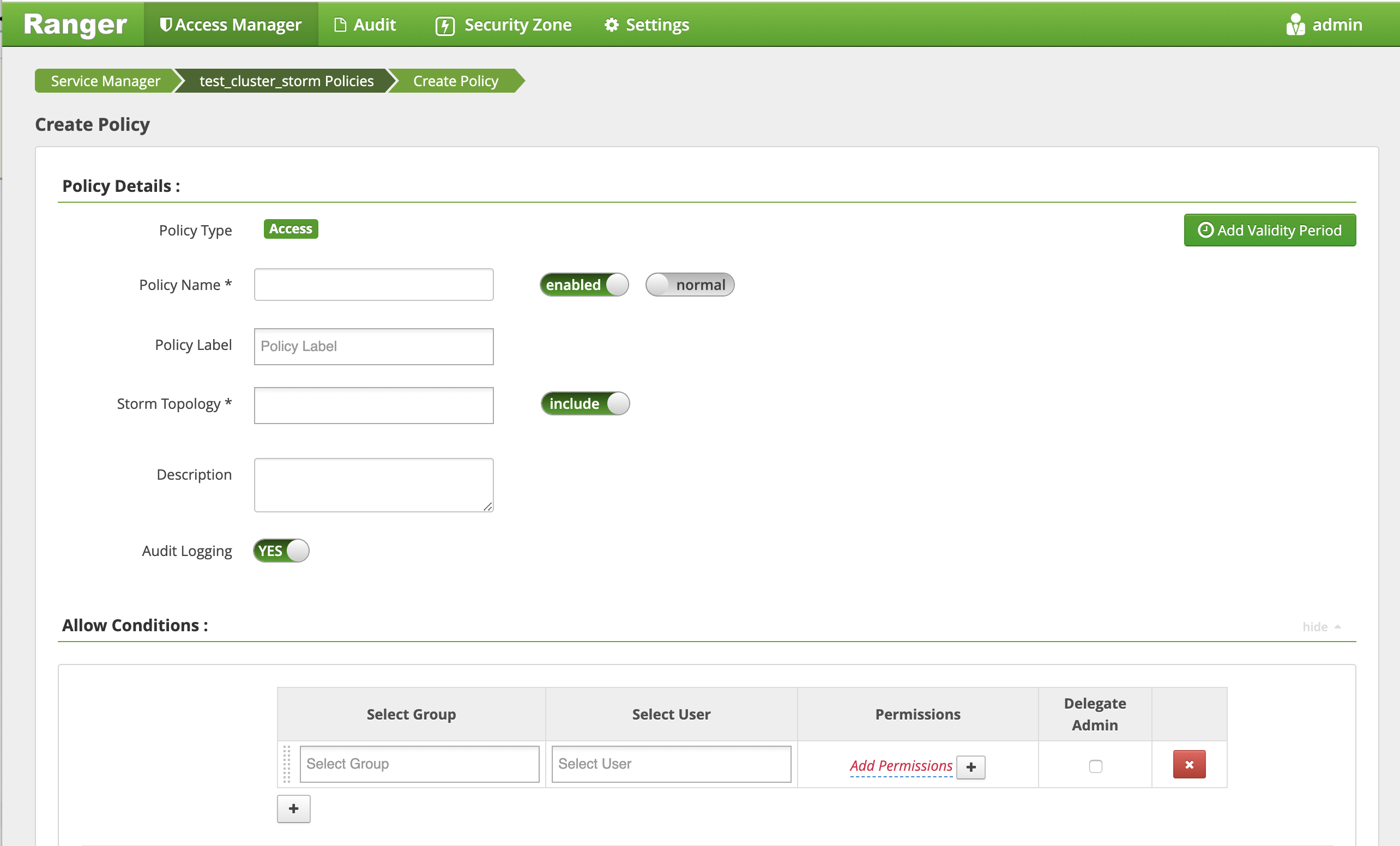
Configure a Resource-based Policy: Storm
How to add a new policy to an existing Storm service.
-
On the Service Manager page, select an existing Storm service.
The List of Policies page appears.
-
Click Add New Policy.
The Create Policy page appears.
-
Complete the Create Policy page as follows:
Table 1. Policy Details Label
Description
Policy Name Enter an appropriate policy name. This name is cannot be duplicated across the system. This field is mandatory. normal/override Enables you to specify an override policy. When override is selected, the access permissions in the policy override the access permissions in existing policies. This feature can be used with Add Validity Period to create temporary access policies that override existing policies. Storm Topology Enter an appropriate Topology Name. Description (Optional) Describe the purpose of the policy. Audit Logging Specify whether this policy is audited. (De-select to disable auditing). Policy Label Specify a label for this policy. You can search reports and filter policies based on these labels. Add Validity Period Specify a start and end time for the policy. Table 2. Allow Conditions Label
Description
Select Group Specify the groups to which this policy applies.
To designate a group as an Administrator, select the Delegate Admin check box. Administrators can edit or delete the policy, and can also create child policies based on the original policy.
The public group contains all users, so granting access to the public group grants access to all users.
Select User Specify the users to which this policy applies.
To designate a user as an Administrator, select the Delegate Admin check box. Administrators can edit or delete the policy, and can also create child policies based on the original policy.
Storm User and Group Permissions* Add or edit permissions. See the table below. Delegate Admin You can use Delegate Admin to assign administrator privileges to the users or groups specified in the policy. Administrators can edit or delete the policy, and can also create child policies based on the original policy. Because Storm does not provide a command line methodology for assigning privileges or roles to users, the User and Group Permissions portion of the Storm Create Policy form is especially important.
Table 3. * Storm User and Group Permissions Actions Description Submit Topology Allows a user to submit a topology. File upload Allows a user to upload files. File Download Allows a user to download files. Kill Topology Allows a user to kill the topology. Rebalance Allows a user to rebalance topologies. Activate Allows a user to activate a topology. Deactivate Allows a user to deactivate a topology. Get Topology Conf Allows a user to access a topology configuration. Get Topology Allows a user to access a topology. Get User Topology Allows a user to access a user topology. Get Topology Info Allows a user to access topology information. Upload New Credential Allows a user to upload a new credential. Select/Deselect All Select or deselect all permissions. - You can use the Plus (+) symbol to add additional conditions. Conditions are evaluated in the order listed in the policy. The condition at the top of the list is applied first, then the second, then the third, and so on.
- Click Add.

