Auto-TLS Requirements and Limitations
Reference information for Auto-TLS requirements, limitations, and component support.
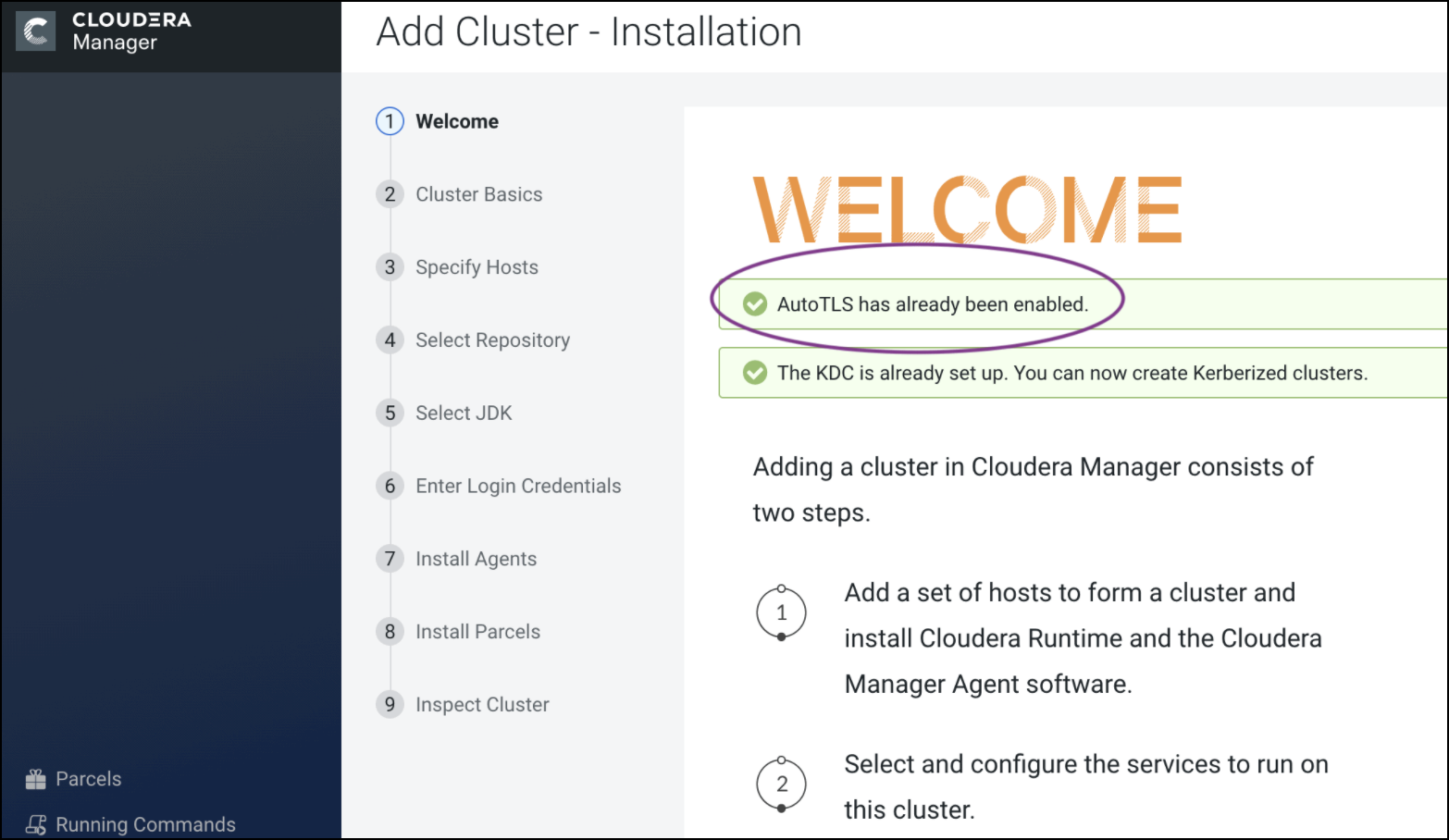
Use Auto-TLS to simplify the process of configuring TLS encryption for Cloudera Manager.
The Auto-TLS feature automates all the steps required to enable TLS encryption at a cluster level. Using Auto-TLS, you can let Cloudera manage the Certificate Authority (CA) for all the certificates in the cluster or use the company’s existing CA. In most cases, all the necessary steps can be enabled easily via the Cloudera Manager UI. This feature automates the following processes –
New Cluster deployment
Summary
The Auto-TLS functionality not only speeds up the initial setup of the wire encryption but also automates future TLS configuration steps for the cluster. The following table summarizes the differences between the available options.
| Steps | HDP/EDH (manual) | CDP Private Cloud use case 1 - Using Cloudera Manager to generate an internal CA and corresponding certificates | CDP Private Cloud use case 2 - Enabling Auto-TLS with an existing Root CA | CDP Private Cloud use case 3 - Enabling Auto-TLS with Existing Certificates |
|---|---|---|---|---|
| Generate CSR | Manual | Automated | Automated | Manual |
| CSR Signed by CA | Manual | Automated | One-time | Manual |
| Deploy certificate to all hosts | Manual | Automated | Automated | Automated |
| Configuration for each service | Manual | Automated | Automated | Automated |
| Cluster restarts | Multiple | Once | Once | Once |
| Configuration steps | Manual | Automated | Automated | Automated |
| New Service steps | Manual | Automated | Automated | Automated |
| New Host cert. generation | Manual | Automated | Automated | Manual |
Reference information for Auto-TLS requirements, limitations, and component support.
Your cluster security requirements may require that you rotate the auto-TLS CA and certificates.
curl -u admin:admin -X POST --header 'Content-Type:
application/json' --header 'Accept: application/json' -d '{
"location": "/opt/cloudera/AutoTLS",
"interpretAsFilenames": true,
"hostCerts": [ {
"hostname": "ccycloud-10.vcdp71.root.hwx.site",
"certificate":
"/tmp/auto-tls/certs/ccycloud-10.vcdp71.root.hwx.site.pem",
"key":
"/tmp/auto-tls/certs/ccycloud-10.vcdp71.root.hwx.site.pem"
} ]
}' 'https://ccycloud-7.vcdp71.root.hwx.site:7183/api/v41/cm/commands/addCustomCerts'
In the example above, the "location" should be omitted if Auto-TLS was enabled or
rotated after 7.1, and the file paths should point to files on the CM server host. curl -u admin:admin -X POST --header 'Content-Type: application/json' --header
'Accept: application/json' -d '{ "sshPort" : 22, "userName" : "root", "password" : "cloudera" }'
'https://ccycloud-7.vcdp71.root.hwx.site:7183/api/v41/hosts/250e1bb7-8987-419c-a53f-c852c275d299/commands/generateHostCerts'
where '250e1bb7-8987-419c-a53f-c852c275d299' in the command above is the hostID.The certificates, keystores, and password files generated by auto-TLS are stored in
/var/lib/cloudera-scm-agent/agent-cert on each Cloudera Manager Agent.
The filenames are as follows:
| Filename | Description |
|---|---|
| cm-auto-global_cacerts.pem | CA certificate and other trusted certificates in PEM format |
| cm-auto-global_truststore.jks | CA certificate and other trusted certificates in JKS format |
| cm-auto-in_cluster_ca_cert.pem | CA certificate in PEM format |
| cm-auto-in_cluster_truststore.jks | CA certificate in JKS format |
| cm-auto-host_key_cert_chain.pem | Agent host certificate and private key in PEM format |
| cm-auto-host_cert_chain.pem | Agent host certificate in PEM format |
| cm-auto-host_key.pem | Agent host private key in PEM format |
| cm-auto-host_keystore.jks | Agent host private key in JKS format |
| cm-auto-host_key.pw | Agent host private key password file |

What kind of feedback do you have?