About Ranger Policies
Ranger Resource-Based Policies
Ranger enables you to Configuring Resource-Based Services (HDFS, HBase, Hive, etc.) and add access policies to those services.
Ranger Tag-Based Policies
Ranger also enables you to create tag-based services and add access policies to those services.
An important feature of Ranger tag-based authorization is the separation of resource-classification from access-authorization. For example, resources (HDFS file/directory, Hive database/table/column etc.) containing sensitive data such as social security numbers, credit card numbers, or sensitive health care data can be tagged with PII/PCI/PHI – either as the resource enters the Hadoop ecosystem or at a later time. Once a resource is tagged, the authorization for the tag would be automatically enforced, thus eliminating the need to create or update policies for the resource.
Using tag-based policies also enables you to control access to resources across multiple Hadoop components without creating separate services and policies in each component.
Tag details are stored in a tag store. Ranger TagSync can be used to synchronize the tag store with an external metadata service such as Apache Atlas.
Tag Store
Details of tags associated with resources are stored in a tag store. Apache Ranger plugins retrieve the tag details from the tag store for use during policy evaluation. To minimize the performance impact during policy evaluation (in finding tags for resources), Apache Ranger plugins cache the tags and periodically poll the tag store for any changes. When a change is detected, the plugins update the cache. In addition, the plugins store the tag details in a local cache file – just as the policies are stored in a local cache file. On component restart, the plugins will use the tag data from the local cache file if the tag store is not reachable.
Apache Ranger plugins download the tag details from the store managed by Ranger Admin. Ranger Admin persists the tag details in its policy store and provides a REST interface for the plugins to download the tag details.
TagSync
Ranger TagSync is used to synchronize the tag store with an external metadata service such as Apache Atlas. TagSync is a daemon process similar to the Ranger UserSync process.
Ranger TagSync receives tag details from Apache Atlas via change notifications. As tags are added to, updated, or deleted from resources in Apache Atlas, Ranger TagSync receives notifications and updates the tag store.
Tags
Ranger Tags can have attributes. Tag attribute values can be used in Ranger tag-based policies to influence the authorization decision.
For example, to deny access to a resource after a specific date:
Add the EXPIRES_ON tag to the resource.
Add an
exipry_datetag attribute and set its value to the expiry date.Create a Ranger policy for the EXPIRES_ON tag.
Add a condition in this policy to deny access when the date specified the in
expiry_datetag attribute is later than the current date.
Note that the EXPIRES_ON tag policy is created as the default policy in tag service instances.
Tags and Policy Evaluation
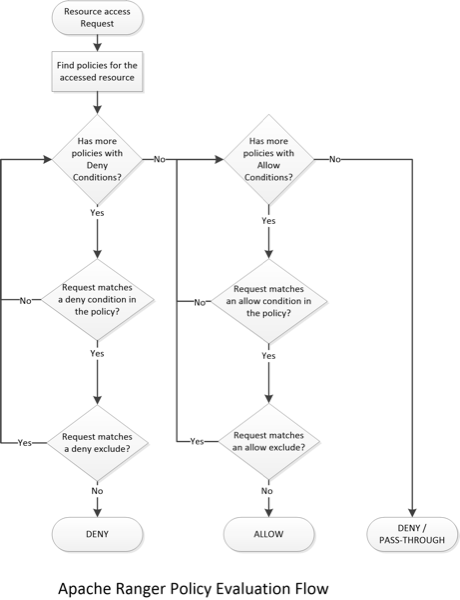
When authorizing an access request, an Apache Ranger plugin evaluates applicable Ranger policies for the resource being accessed. The following diagram shows the details of the policy evaluation flow. More details on the steps in this workflow are provided in the subsequent sections.
[D]
Finding Tags
Apache Ranger supports a service to register context enrichers, which are used to update context data to the access request.
The Ranger Tag service, which is part of the tag-based policies feature, adds a context enricher named RangerTagEnricher. This context enricher is responsible for finding tags for the requested resource and adding the tag details to the request context. This context enricher keeps a cache of the available tags; while processing an access request, it finds the tags applicable for the requested resource and adds the tags to the request context. The context enricher keeps the cache updated by periodically polling Ranger Admin for changes.
Evaluating Tag-Based Policies
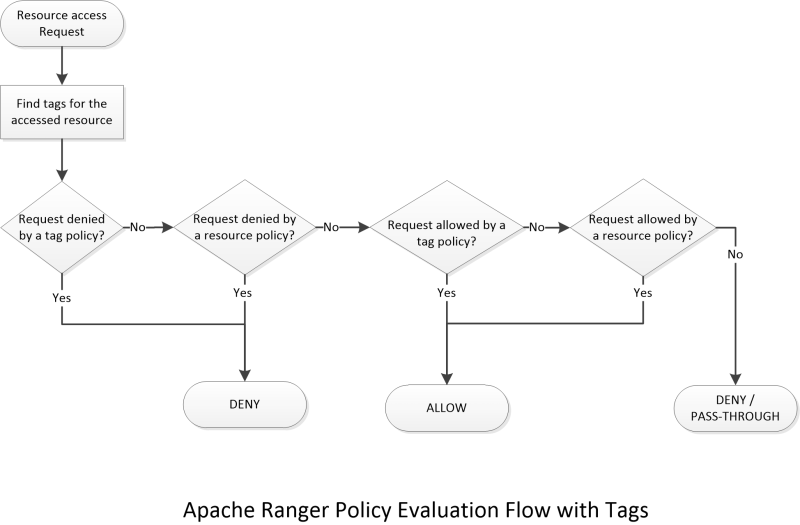
Once the list of tags for the requested resource is found, the Apache Ranger policy engine evaluates the tag-based policies applicable to the tags. If a policy for one of these tag results in a deny, access will be denied. If none of the tags are denied, and if a policy allows for one of the tags, access will be allowed. If there is no result for any tag, or if there are no tags for the resource, the policy engine will evaluate the resource-based policies to make the authorization decision.
Using Tags in Conditions
Apache Ranger allows the use of custom conditions while evaluating authorization policies. The Apache Ranger policy engine makes various request details – such as user, groups, resource, and context – available to the conditions. Tags in the request context, which are added by the enricher, are available to the conditions and can be used to influence the authorization decision.
The default policy in tag service instances, the EXPIRES_ON tag, uses such condition to check to see if the request date is later than the value specified in tag attribute expiry_date. This default policy does not work unless an EXPIRES_ON tag has been created in Atlas.
Apache Ranger Access Conditions
The Apache Ranger access policy model consists of two major components:
Specification of the resources a policy is applied to, such as HDFS files and directories, Hive databases. tables. and columns, HBase tables, column-families, and columns, and so on.
Specification of access conditions for specific users and groups.
Allow, Deny, and Exclude Conditions
Apache Ranger supports the following access conditions:
Allow
Exclude from Allow
Deny
Exclude from Deny
These access conditions enable you to set up fine-grained access control policies.
For example, you can allow access to a "finance" database to all users in the "finance" group, but deny access to all users in the "interns" group. Let's say that one of the members of the "interns" group, "scott", needs to work on an assignment that requires access to the "finance" database. In that case, you can add an Exclude from Deny condition that will allow user "scott" to access the "finance" database. The following image shows how this policy would be set up in Apache Ranger:
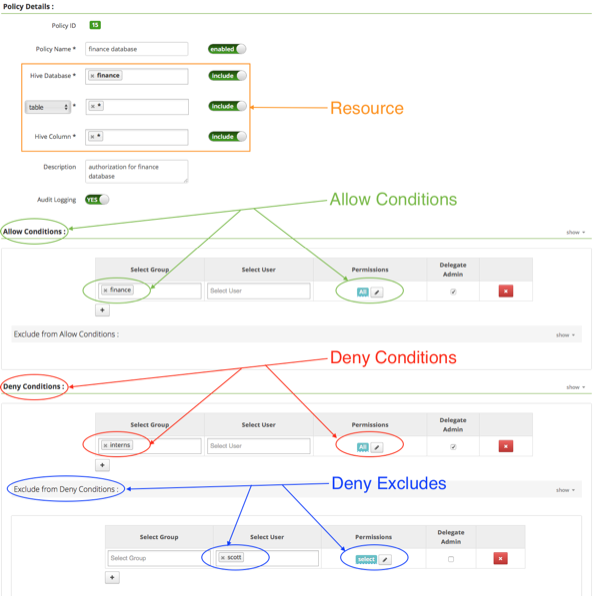
[D]
If Deny Conditions does not appear on your Policy Details page, you must first Enable Deny Conditions for Policies.
Enable Deny Conditions for Policies
The deny condition in policies is disabled by default and must be enabled for use.
From Ambari>Ranger>Configs>Advanced>Custom ranger-admin-site, add
ranger.servicedef.enableDenyAndExceptionsInPolicies=.trueRestart Ranger.