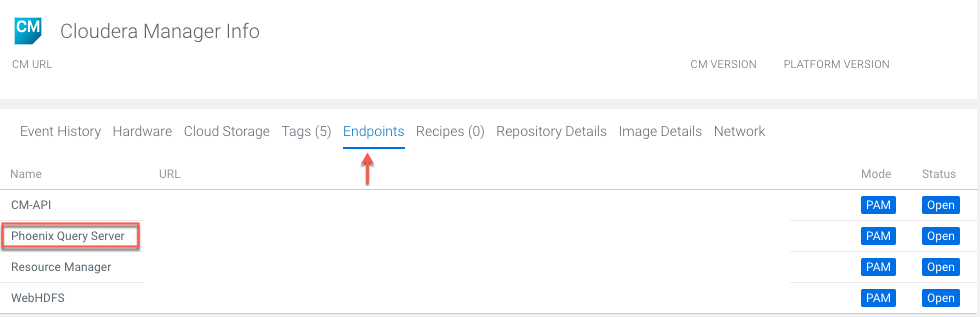
Connect to Phoenix Query Server through Apache Knox
You can connect to Phoenix Query Server (PQS) using the JDBC thin client through the Apache Knox gateway. Apache Knox requires your thin client connection to be over HTTPS.
Ensure that you have access to Apache Phoenix and Apache HBase, and you have the required permissions configured in Ranger to connect to PQS.
jdbc:phoenix:thin:url=https://[***https://pqs.knox.endpoint:8443/gateway/cdp-proxy-api/avatica/***]:[***8765***] /[***clusteropdb***]/cdp-proxy-api/avatica/;serialization=PROTOBUF; authentication=BASIC;avatica_user=[***WORKLOADUSERNAME***] ;avatica_password=[***WORKLOADPASSWORD***] ;truststore=[***/home/path/truststore.jks***];truststore_password=[***TRUSTSTOREPASSWORD***]