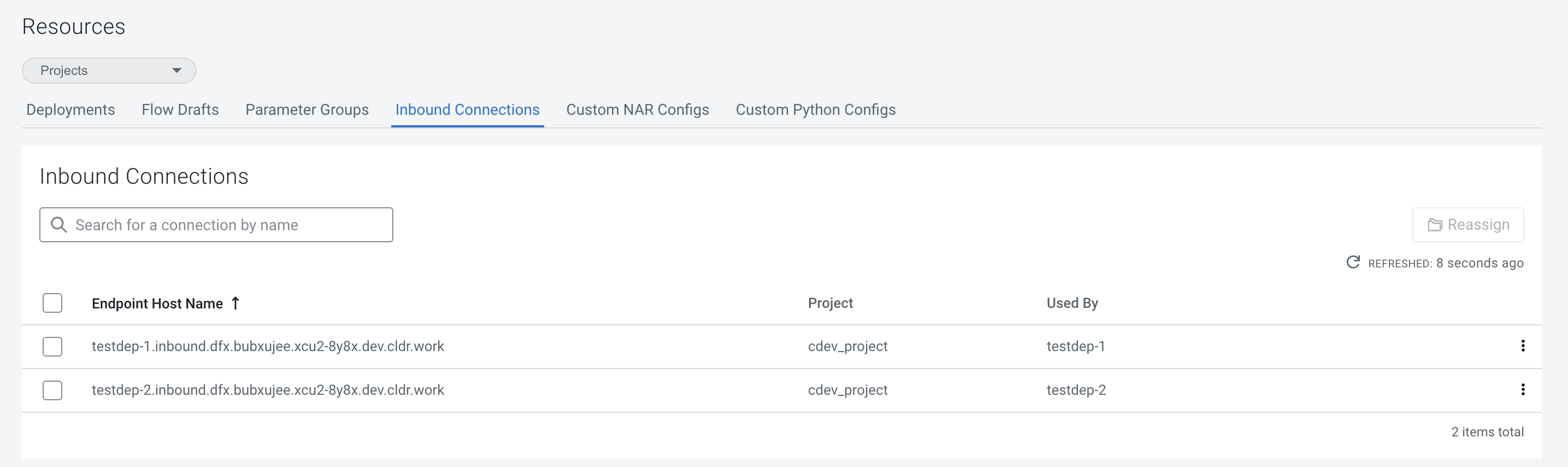
Inbound connections
An Inbound Connection Endpoint allows you to stream data from an external source application to a flow.
An Inbound Connection Endpoint provides a stable hostname that can be used to send data to a Cloudera Data Flow deployment located in the same environment. You can create an Inbound Connection Endpoint during deployment, provided that the flow definition supports creating such endpoints.
Endpoints exist within the environment where they were created. They cannot be moved between environments. If the environment is deleted, the endpoint gets deleted as well, and cannot be reused.
One endpoint can be assigned to one deployment at a time. To reassign an existing inbound connection endpoint, you need to first terminate the deployment to which it is currently assigned, then assign the existing endpoint to a new deployment in the NiFi configuration step during flow deployment.
Setting up an Inbound Connection Endpoint is a complex task, affecting how you develop a flow definition in NiFi and how you deploy it in Cloudera Data Flow. Once your flow has been deployed, you need to configure your client, be it directly an external application or through an external load balancer, to communicate with the Inbound Connection Endpoint of your flow deployment.
Adding an inbound connection to an existing deployment
Learn how to add an inbound connection to an existing deployment.
Renewing the certificate for an inbound connection endpoint
If you need to replace an X.509 certificate for an inbound connection endpoint before it expires, you can do so manually.
- If you have renewed the NiFi Inbound SSL Context Service:
- You have to take no further action.
- If you have renewed the Client SSL Context:
- After your Cloudera Data Flow deployment has restarted, you switch to the NiFi Configuration pane to download the Client Certificate and the Client Private Key. You can then add these to your client.
Reassigning an inbound connection endpoint to a different project
Learn how to reassign an inbound connection to another project.
- Make sure that you have DFDeveloper permission to perform this task. For information on account and resource roles, see Cloudera Data Flow Authorization.
You cannot reassign an inbound connection that is currently used by a deployment. You have to terminate the deployment using it making sure that the Delete assigned endpoint hostname option is not selected before you can reassign it to a different project.
Using Inbound Connections with an external load balancer
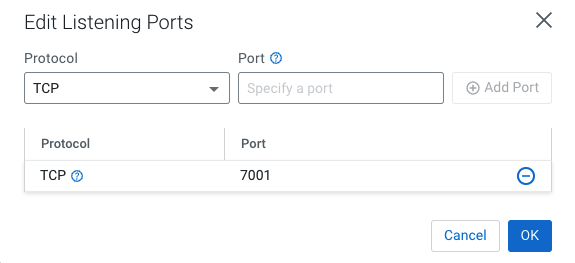
Once a Cloudera Data Flow deployment with an Inbound Connection Endpoint
is available, you can go on and connect an external load balancer to start sending data.
Inbound Connection Endpoints are created in Cloudera Data Flow with an internal Layer 4 (L4) load balancer (LB). Nevertheless, it is also possible to use your own native Layer 7 (L7) LB (Application Gateway on Azure, Application Load Balancer on AWS, respectively) in front of the Cloudera managed L4 LB.
Cloudera recommends achieving this by
configuring your L7 LB to use the Cloudera Data Flow deployment LB as a backend.
Enabling TLS between your LB and the Cloudera Data Flow LB is recommended, but
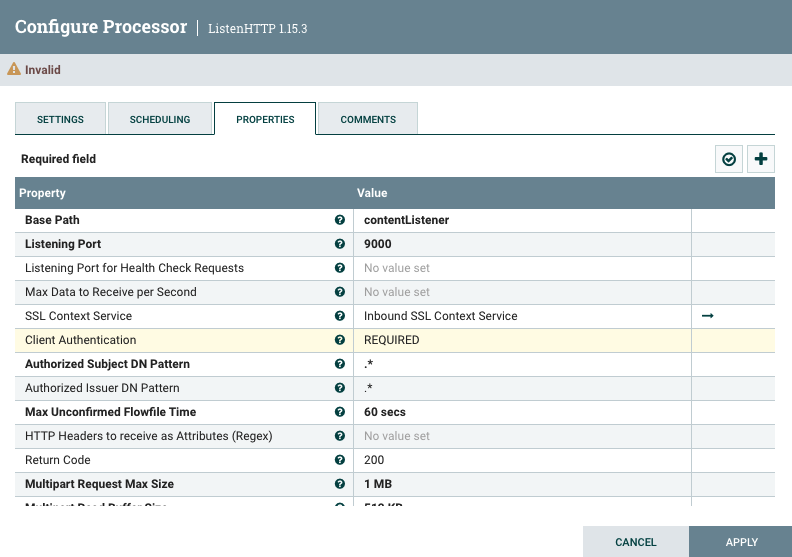
mTLS is not possible for the backend connection. This means that your Listen Processor (e.g.,
ListenHTTP) in your NiFi flow cannot be configured with Client Auth = Required
when using an external LB as a gateway.
You may configure the listening side of your LB and routing rules according to the requirements of your organization.
Alternatively, you may be required to use a L4 LB provided by your organization in front of the Cloudera managed LB. This is also possible, although Cloudera recommends directly using the Cloudera managed L4 LB when possible.
Typically, when using an external load balancer to act as a gateway, the internal managed load balancer should stay private. This can be accomplished by deselecting the “Use Public Endpoint” option when enabling Cloudera Data Flow for your environment, which limits Cloudera Data Flow to only use private subnets for all resources. If public access is needed, that would be done by exposing private resources via the external gateway load balancer.
Configuration workflow
Currently, an Inbound Connection Endpoint can only be created during flow deployment, and cannot be reassigned without terminating the flow deployment for which it was created.
To configure an external load balancer, you need to go through the following steps:
Configure an Application Gateway in Azure
Learn about the settings required to set up an Azure Application Gateway to communicate with an Inbound Connection Endpoint.
Create an Azure Application Gateway service (you find it in the Networking services category) using the following settings:
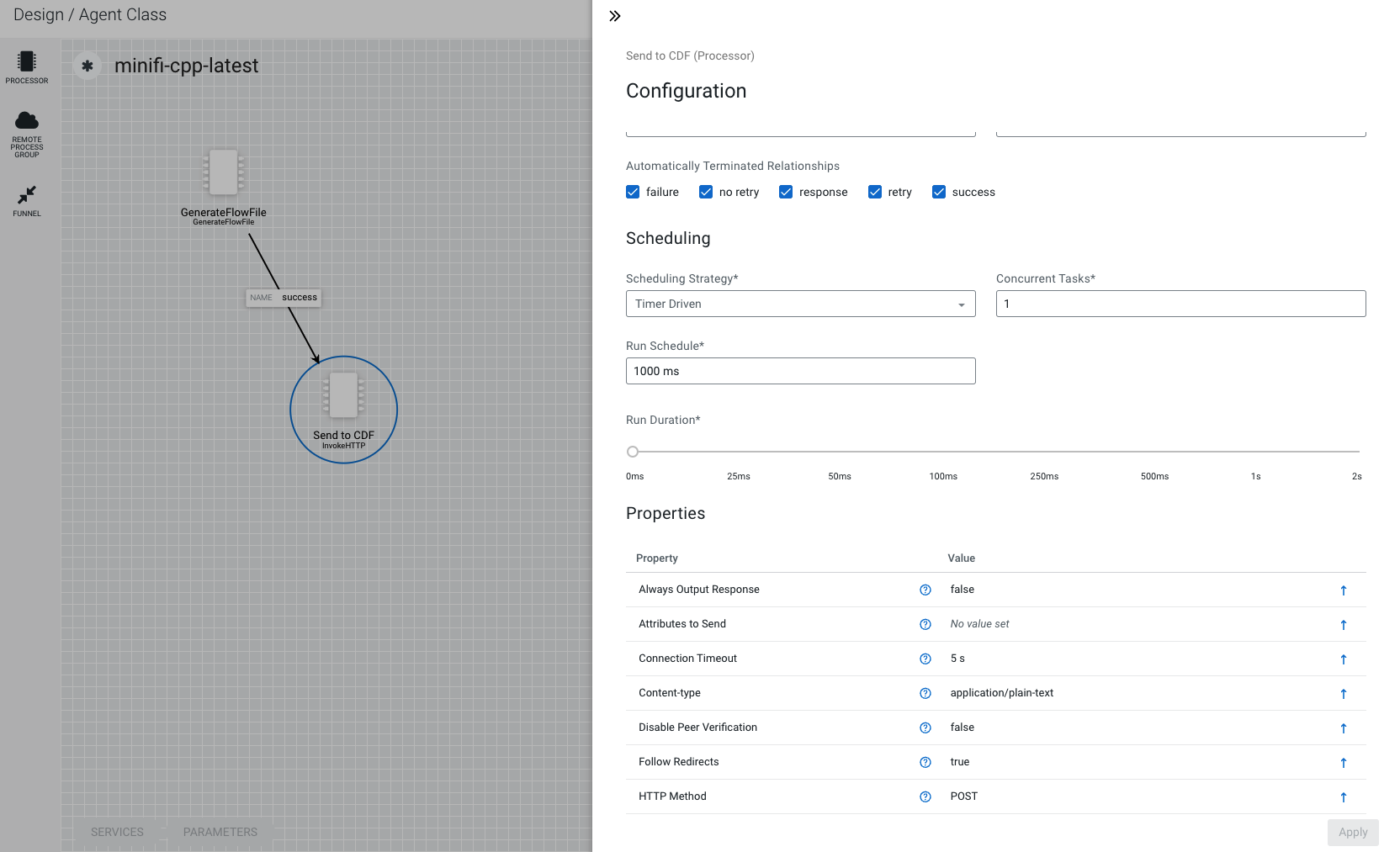
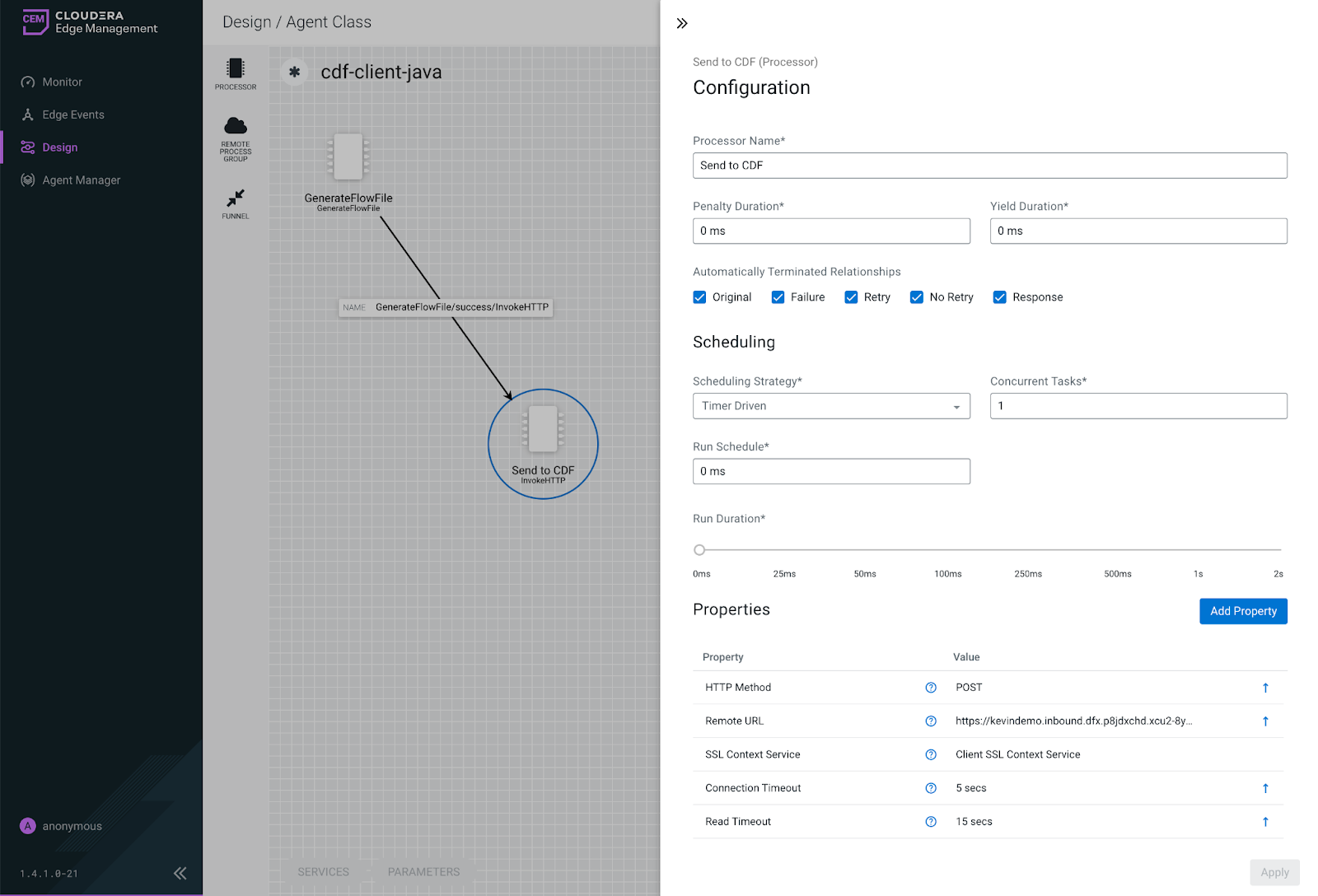
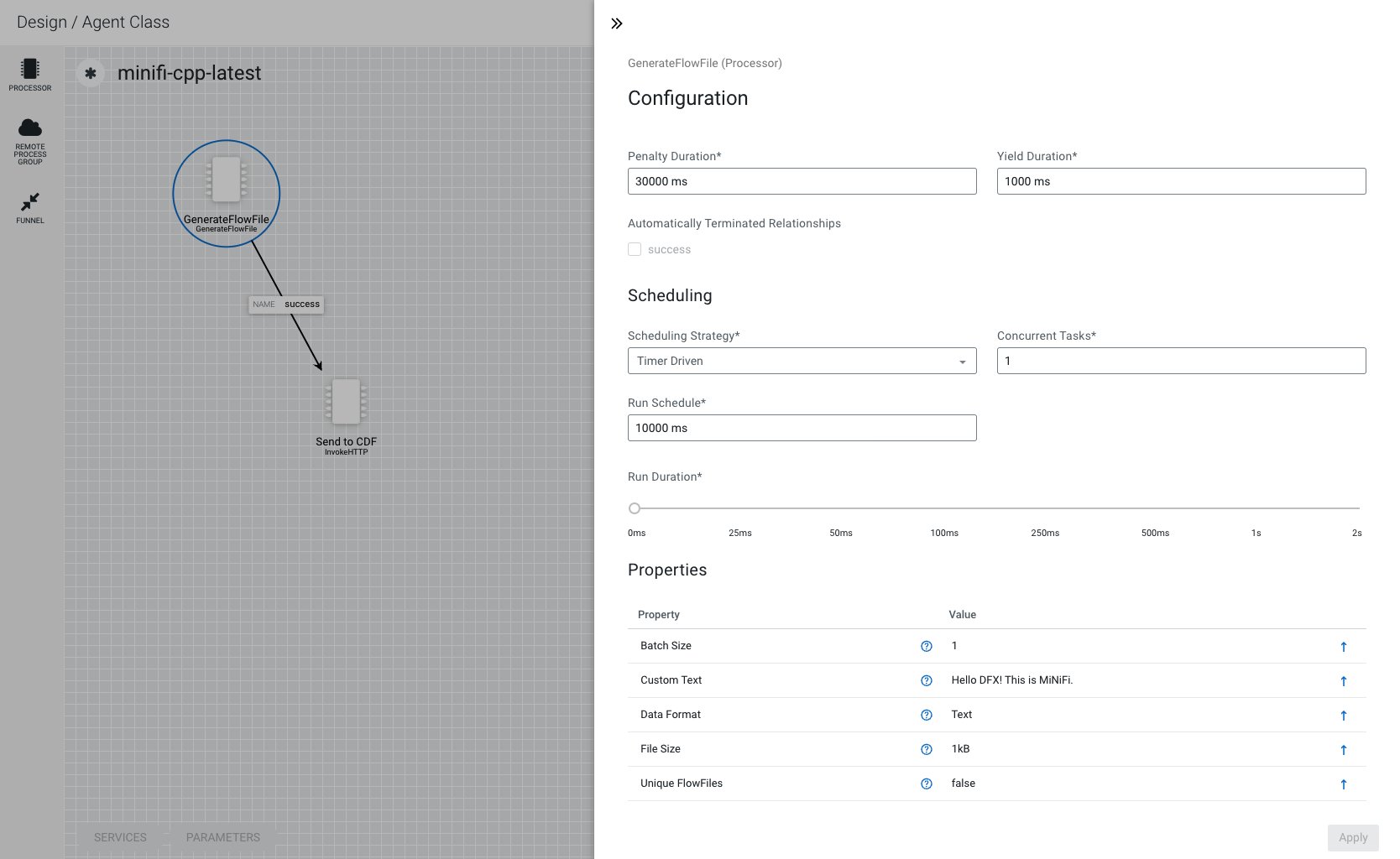
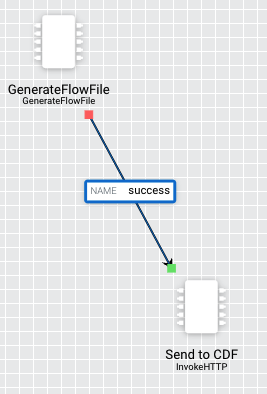
Tutorial: MiNiFi to Cloudera Data Flow flow deployment
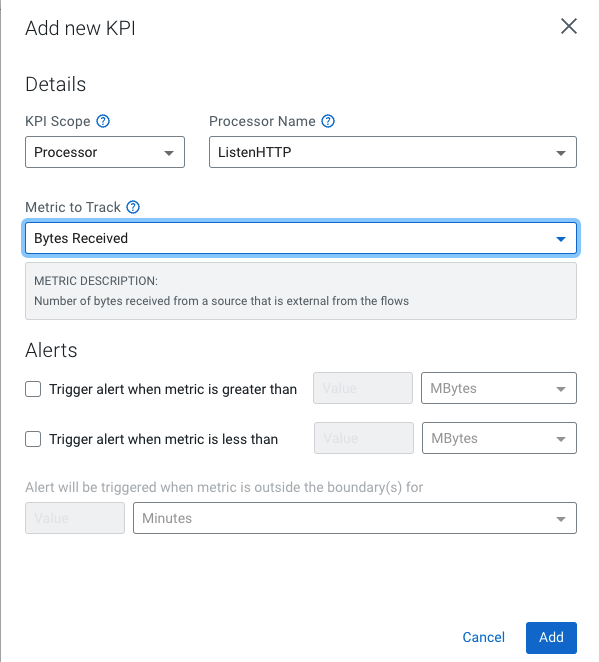
This tutorial walks you through creating an inbound connection endpoint in Cloudera Data Flow used by a flow deployment to receive data from one or more MiNiFi agents managed by Edge Flow Manager.
Tutorial: Invoking an HTTP endpoint with curl
This tutorial walks you through invoking an HTTP Inbound Connection Endpoint with curl using the ListenHTTP filter to Kafka ReadyFlow from the ReadyFlow Gallery.
Connecting applications to an endpoint
Once a Cloudera Data Flow deployment with inbound connection is available, you can go on and connect an external application to start sending data.
-
A deployment with inbound connection is available.
-
A network connection through which the client can reach the deployment endpoint is available.
- You have been assigned at least the DFFlowUser role for the environment to which you want to configure the inbound connection.
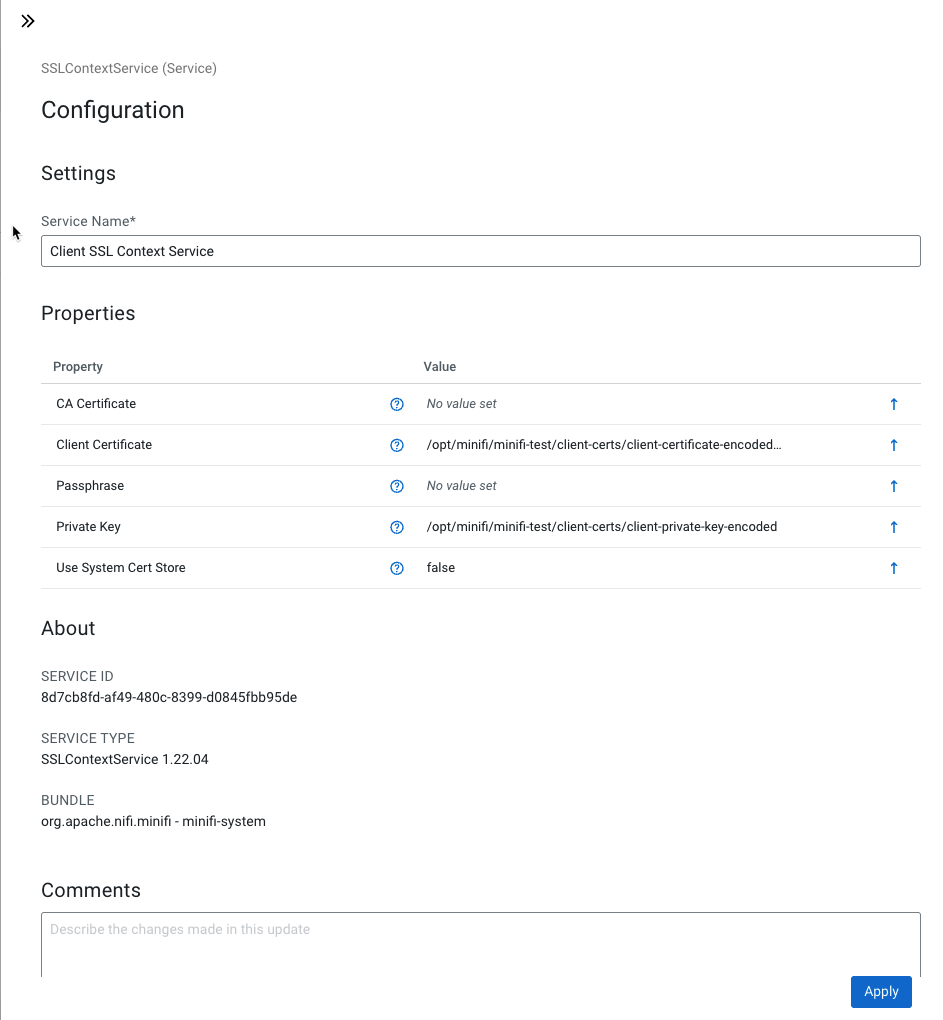
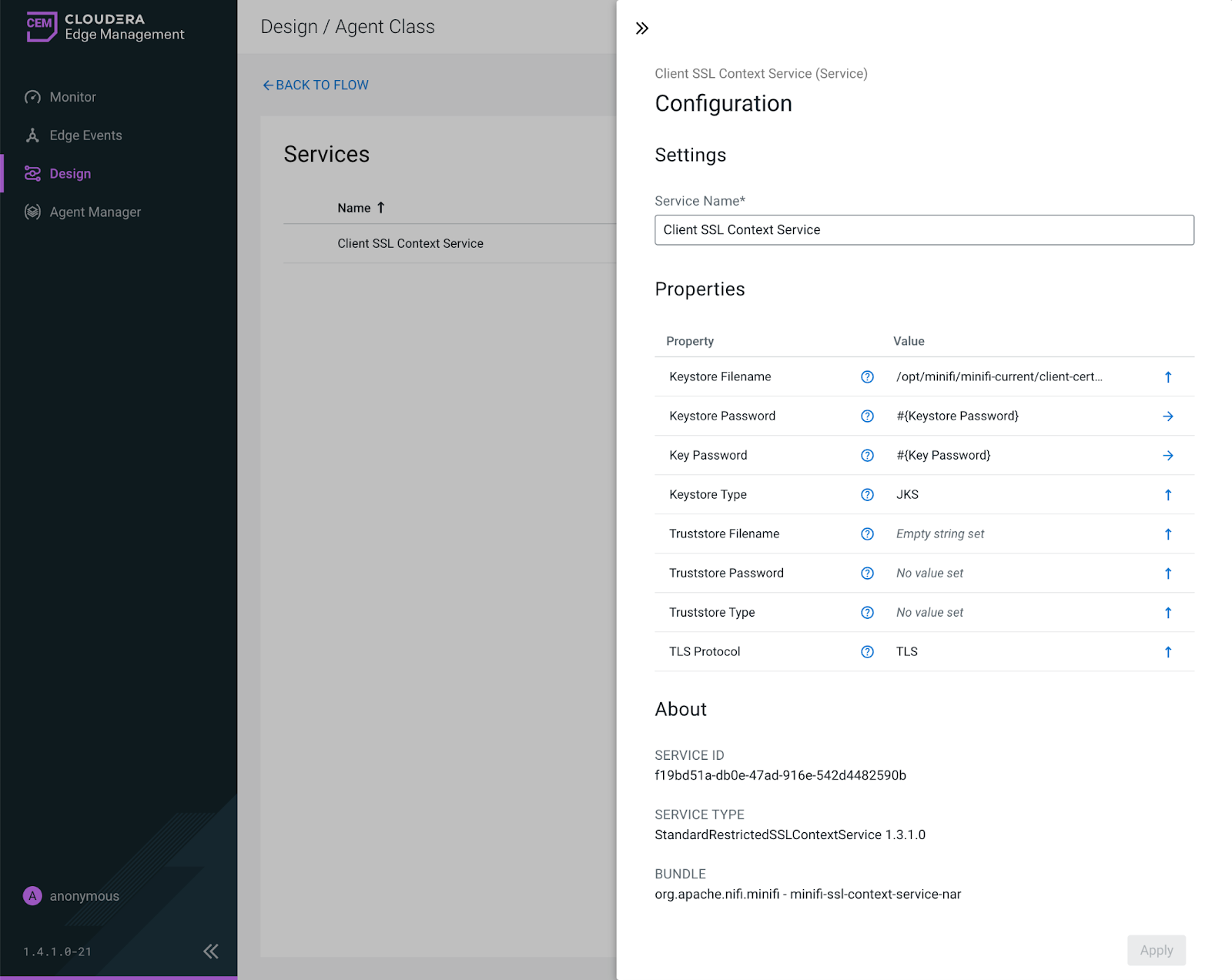
TLS keys and certificates
When using Inbound Connection Endpoints, sensitive information is sent over the network between Cloudera Data Flow (CDF) and external data sources including configuration files that contain passwords. To secure this transfer, Cloudera strongly recommends that you configure mutual Transport Layer Security (TLS) encryption.
TLS is an industry standard set of cryptographic protocols for securing communications over a network.
Configuring TLS involves creating a private key and a public key for use by server and client processes to negotiate an encrypted connection. In addition, TLS can use certificates to verify the trustworthiness of keys presented during the negotiation to prevent spoofing and mitigate other potential security issues.
 Apply Changes
Apply Changes